What You Should Know About SecOps in Modern Security
Is your organization struggling to secure its operations effectively? This blog post explains the role of SecOps in modern security, examines the benefits of integrating advanced IT tools, and outlines best practices for cultivating a robust security culture. Business owners will gain practical insights that help reduce risks and strengthen overall operational resilience.

Understand the Role of SecOps in Modern Security Frameworks
SecOps integrates security operations within cyber defense, outlining team responsibilities that include managing a threat intelligence platform and user behavior analytics while assessing the link between SecOps and DevOps. Professionals require distinct skills and practices, such as network detection and response, to address common challenges and drive innovation.
Define SecOps and Its Importance in Cyber Defense
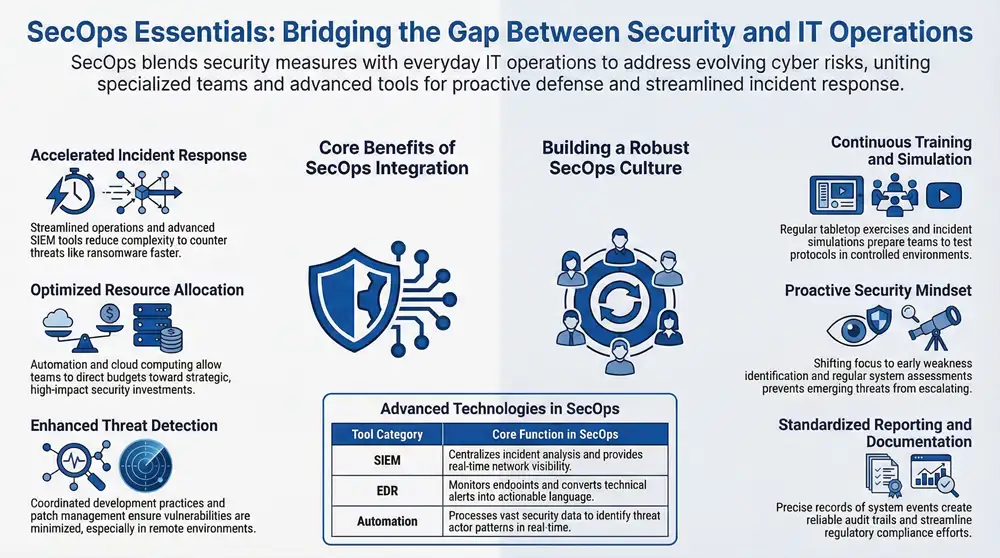
SecOps represents a framework that blends security measures with everyday IT operations management. This process uses ongoing research to monitor computer systems and support mobile application security while ensuring robust defenses across the internet.
SecOps addresses evolving cyber risks by uniting specialized teams and refined management practices. The framework improves the protection of digital assets through practical methods that maintain computer security and safeguard mobile application security in an internet-connected environment.
Identify Key Responsibilities of SecOps Teams
SecOps teams manage day-to-day security monitoring and perform thorough threat analysis to support a robust managed security service. They collaborate with software development units to incorporate secure practices into operational tasks, ensuring smooth evolution in security measures and improved productivity.
These teams establish procedures for rapid incident response and maintain clear communication channels to swiftly address vulnerabilities. Their responsibilities also include regular system reviews and proactive updates of security protocols, which uphold effective security monitoring and efficient managed security service operations amid ongoing changes.
Explore the Relationship Between SecOps and DevOps
SecOps and DevOps work together to integrate security measures within the development cycle using precise orchestration techniques. Organizations employ advanced software to monitor mobile app performance and server stability, allowing the chief information security officer to maintain comprehensive oversight.
This collaboration unites security and development efforts for efficient incident handling and risk management. Coordinated practices support software integrity and safeguard mobile app functionality on servers, enabling the chief information security officer to respond swiftly to emerging vulnerabilities.
Recognize the Skills Required for SecOps Professionals
SecOps professionals must exhibit the ability to analyze machine data to pinpoint potential threats effectively. Their expertise in network security combines with hands-on experience from red team exercises to identify and address vulnerabilities.
A solid grasp of devops practices enables these experts to integrate security protocols into routine operations seamlessly. Mastery in running a security operations center supports ongoing threat identification and fosters reliable system protection.
Examine Tools Utilized by SecOps Teams
SecOps teams use advanced technology to monitor network systems and quickly resolve security incidents. They implement tools such as microsoft intune to manage devices within digital transformation efforts and support proactive security processes.
These teams set up integrated systems to provide real-time alerts and precise incident tracking, ensuring swift responses when threats arise. Their approach combines reliable technology with well-defined protocols for robust secops performance and continuous operational safety.
Discuss Common Challenges Faced by SecOps
SecOps teams face challenges when processing vast amounts of security data collected from many endpoints, which can complicate their task of pinpointing true threats. They rely on extended detection and response systems to meet the goal of efficient vulnerability management despite the increasing volume of incoming alerts.
Regulatory compliance requirements demand rigorous attention to detail, often straining resources and complicating routine monitoring efforts. Teams continuously adjust their procedures to integrate strict protocol adherence with robust vulnerability management, ensuring that security measures remain effective and responsive.
Assess the Benefits of Integrating SecOps Into Your Organization

Integrating SecOps streamlines incident response while boosting collaboration between security and operations teams. It refines threat detection and remediation, supports regulatory compliance, and optimizes resource allocation for security investments. This approach harnesses advanced intelligence and artificial intelligence insights to curb cybercrime, ensuring improved data security as engineers adjust critical processes.
Increase Incident Response Efficiency Through SecOps
SecOps integration boosts incident response efficiency by streamlining operations and reducing overall complexity. Advanced SIEM tools offer real-time analysis of the attack surface while refining identity management protocols, which helps teams quickly detect and counter threats such as ransomware.
This approach equips organizations with actionable insights and practical expertise to accelerate incident resolution. By optimizing SIEM and identity management processes, businesses can better control their attack surface and swiftly address security breaches including ransomware.
Strengthen Collaboration Across Security and Operations
An effective synergy between security and operations teams results in improved incident response and minimized downtime. Working in a unified manner, professionals use security information and event management tools to monitor firewall activity while integrating threat intelligence insights for rapid resolution of emerging incidents.
Organizations benefit from aligned work processes that promote clear communication and coordinated action when facing security challenges. Teams jointly refine incident response procedures, optimize firewall configurations, and apply threat intelligence data to prevent excessive downtime, ensuring seamless support for business systems.
Improve Threat Detection and Remediation Processes
SecOps teams improve threat detection by implementing strong patch management that minimizes vulnerabilities and supports effective information security. Clear communication among departments and coordinated development practices play a critical role in identifying potential threats, especially for organizations with remote work arrangements.
Active monitoring systems combined with transparent communication channels enable teams to quickly address risks and refine remediation procedures. Coordinated efforts between development units and security specialists ensure that patch management processes remain effective and that remote work environments continue to operate securely.
Facilitate Compliance With Regulatory Requirements
The integration of SecOps streamlines compliance with regulatory requirements through continuous system assessments and the implementation of features such as passwordless authentication, which builds comprehensive knowledge and helps detect every potential threat. This method improves speed in adapting to compliance changes while keeping a secure security landscape that meets established mandates.
SecOps supports organizations in meeting regulations by standardizing security protocols that facilitate rapid responses and maintain steady speed when addressing evolving threats. The approach uses advanced monitoring tools and expert-driven insights to provide a clear knowledge base within a dynamic landscape, ensuring adherence to all compliance standards.
Optimize Resource Allocation for Security Investments
SecOps integration assists organizations in directing budgets toward strategic investments while reducing unnecessary expenditures. The use of automation, cloud computing, and endpoint detection and response systems enables teams to counter cyber threats with precision and cost effectiveness.
Industry experts underscore these advantages in a well-prepared white paper that outlines practical improvements in resource allocation. Focused spending on integrated security operations allows businesses to invest further in advanced tools for real-time threat monitoring.
Enhance Overall Security Posture With SecOps Practices
SecOps practices bolster an organization’s security posture by uniting cloud security measures with structured monitoring routines. Employing a specialized tool that integrates API data with SOAR features, security teams detect threats swiftly and maintain safe operations within the cloud.
Organizations benefit from streamlined risk management when they link traditional systems to expansive cloud setups. Expert teams use robust tools with API connectivity and SOAR modules to monitor cloud environments effectively, ensuring a secure and agile defense against emerging challenges.
Identify Key Tools and Technologies Supporting SecOps
This section reviews key tools that support SecOps in modern security frameworks. It examines security information and event management solutions, automation tools that streamline processes, and threat intelligence platforms critical for data breach prevention. Endpoint detection and response technologies, network monitoring systems, and cloud security measures illustrate a solid approach to security orchestration, operational efficiency, and continuous learning for socs.
Explore Security Information and Event Management Solutions
Security Information and Event Management solutions offer real-time monitoring that boosts visibility across an organization’s network. These systems centralize incident analysis, breaking down data silo barriers while reducing the reliance on outsourcing and ensuring precise authentication tracking.
Industry experts note that SIEM tools empower organizations by delivering actionable insights from authentication logs and other critical alerts. The clear view provided by these solutions allows teams to address vulnerabilities efficiently and maintain secure operations within the organization.
Discover Automation Tools That Streamline SecOps
Automation tools streamline SecOps processes by efficiently processing vast amounts of security information. They analyze threat actor behavior and reinforce application security using a proven methodology that significantly improves an organization’s security posture.
These solutions enable rapid incident responses and facilitate continuous updates to the security posture in real time. They offer actionable information on threat actor patterns while supporting a structured methodology that sustains robust application security across operations.
Analyze Threat Intelligence Platforms for SecOps
Threat intelligence platforms provide security teams with comprehensive visibility through configurable dashboard interfaces that display real-time alerts and system performance metrics. They integrate data from AWS logs and other key sources, enabling effective system monitoring and accurate root cause analysis that supports robust IT service management.
These platforms simplify threat data correlation by automating the consolidation of alerts and notifications within a unified system. Their advanced dashboard capabilities allow for precise root cause analysis while reinforcing IT service management practices, ensuring that security monitoring on AWS remains efficient and reliable.
Evaluate Endpoint Detection and Response Technologies
Endpoint detection and response technologies support security operations by continuously monitoring endpoints and flagging unusual activities. Their systems convert technical alerts into clear language, enabling teams to address risk swiftly and protect each key asset.
These solutions integrate detection and response capabilities with real-time monitoring to reduce potential risk effectively. They transform complex technical data into straightforward language that strengthens security operations and secures essential asset integrity.
Investigate Network Monitoring Tools for Better Visibility
Efficient network monitoring tools deliver clear visibility across an organization’s IT infrastructure. They enable security teams to promptly address network anomalies and streamline patch processes while ensuring that endpoint security measures comply with established policy.
These systems provide real-time insights that equip teams to triage issues quickly and implement corrective actions effectively. By consolidating data and simplifying incident analysis, they support proactive approaches that maintain system integrity and overall network stability.
Understand the Role of Cloud Security in SecOps
Cloud security integrates with SecOps frameworks to improve efficiency and refine threat detection across network systems. The solid integration supports soc operations by employing bmc software solutions that protect critical infrastructure during continuous monitoring.
Organizations use cloud security to maintain precise visibility over system activity and ensure prompt incident response. Technical teams combine cloud-based measures with soc analytics and bmc software insights to safeguard critical infrastructure while optimizing overall efficiency.
Learn Best Practices for Building a SecOps Culture
Fostering effective teamwork and clear documentation methods, a robust SecOps culture emphasizes strong inter-team communication, continuous training, incident simulation, and proactive cyberattack hunting. Practical programs address vulnerability issues and emerging machine learning trends while utilizing internet of things technology. Recognizing team achievements drives a comprehensive approach to modern security operations.
Foster Strong Communication Between Teams
Robust communication between SecOps teams establishes a foundation that supports efficient workflow and timely sharing of essential intel. This approach directs attention to maintaining a solid infrastructure and aligns with best practices observed in google security operations, ensuring that all team members are informed and responsive.
Regular briefings and clear communication channels help integrate actionable intel throughout the security workflow. By cultivating an environment where direct dialogue is valued, organizations strengthen their overall infrastructure and support initiatives rooted in google security operations with focused attention on every detail.
Implement Continuous Training and Development Programs
SecOps teams benefit from regular training sessions that refresh their technical skills and update their knowledge of cyber security practices. Continuous training programs support operational readiness by equipping team members to address evolving threats and manage risks effectively.
Development programs offer focused lessons that connect practical applications with current security protocols. These initiatives blend hands-on exercises with updated risk management techniques, ensuring that SecOps personnel maintain a strong foundation in modern security operations.
Encourage Incident Simulation and Tabletop Exercises
Incident simulation and tabletop exercises offer security teams a controlled environment to practice response strategies while testing the effectiveness of their protocols. These practices allow teams to identify gaps and refine operational workflows that directly support a strong SecOps framework.
Tabletop exercises build clarity among team members and improve communication during simulated security events. Such drills provide actionable insights to adjust response tactics and prepare the organization for actual cybersecurity incidents.
Promote a Proactive Mindset in Security Operations
Organizations that rely on managed IT services and office equipment benefit when security teams adopt a proactive mindset. A forward-thinking approach in security operations allows teams to spot potential weaknesses early and address emerging threats promptly.
Regular system assessments and focused training sessions keep security personnel prepared to respond quickly to risks. This proactive strategy proves invaluable in maintaining secure business environments and ensuring reliable IT service operations.
Establish Clear Documentation and Reporting Processes
Clear documentation and precise reporting processes form a solid foundation that supports secure operations and effective audit trails. Organized records of system events and incident responses offer clear insights, enabling teams to quickly identify concerns and adjust security measures with confidence.
Established documentation methods streamline compliance efforts and provide a reliable reference during external reviews. Consistent reporting practices allow IT professionals and business owners to track incident trends and refine procedures, ensuring reliable operational security.
Recognize and Reward SecOps Achievements
Recognizing accomplishments within SecOps teams boosts motivation and reinforces commitment to robust security practices. Structured reward initiatives encourage effective incident handling and drive continual improvements in cybersecurity and IT services.
Reward programs offer clear incentives for achieving performance benchmarks while maintaining operational excellence in security operations. This approach fosters a culture where every successful action contributes to stronger security measures and more efficient IT service management.
Examine Real-World Case Studies of Effective SecOps
SecOps case studies highlight successful implementations at Fortune 500 firms, lessons learned from failures, and the impact of cyber attacks. They detail industry-specific security strategies, innovations driving SecOps solutions, and insights from leaders on best approaches. This overview connects to practical examples that inform managed cybersecurity and IT service practices.
Analyze Successful SecOps Implementation in Fortune 500 Firms
Fortune 500 companies set a benchmark in security operations with their robust SecOps implementations. These organizations use real-time monitoring systems and advanced endpoint detection to identify threats early, ensuring that their IT environments remain secure and responsive to potential risks.
Industry experts observe that successful SecOps strategies hinge on clear communication channels and precise incident analysis. This approach offers actionable insights for businesses aiming to improve managed cybersecurity practices and maintain strong overall IT security.
Review Lessons Learned From SecOps Failures
Case studies indicate that SecOps failures often stem from lapses in communication and unclear operational procedures, leading to delayed threat detection and slower incident responses. Lessons learned from these experiences urge organizations to refine their incident tracking protocols and update cybersecurity strategies regularly.
Organizations observed that misaligned resources and outdated monitoring tools contribute significantly to security shortfalls. Experiences from these shortcomings prompt IT teams to invest in advanced network monitoring and strengthen operational coordination to support reliable managed security services.
Discuss the Impact of Cyber Attacks on SecOps Practices
Cyber attacks challenge established SecOps protocols by exposing vulnerabilities and testing the agility of incident response systems. Organizations feel pressure to adjust their monitoring frameworks as targeted breaches push teams to refine threat detection strategies.
Real-world case studies indicate that significant cyber incidents drive shifts in IT security practices, prompting teams to update response plans and integrate improved tracking tools. These experiences offer actionable insight, guiding IT teams toward more efficient remediation and risk management techniques.
Understand Industry-Specific SecOps Strategies
Industry-specific SecOps strategies address the distinct needs of organizations that rely on managed IT services and office equipment solutions. Businesses with extensive operational experience adopt tailored security operations to align with unique risk profiles, ensuring robust protection and efficient service delivery in environments where data sensitivity is a priority.
Real-world case studies show that focused SecOps practices improve threat identification and streamline incident response for niche industries. Insights from experienced professionals illustrate that adjusting security protocols to match specific operational challenges reduces system downtime and maintains secure IT service performance for organizations in specialized sectors.
Highlight Innovations Driven by SecOps Solutions
Several case studies demonstrate that SecOps solutions have introduced practical automation features that refine threat detection and improve response times. Real-world examples reveal that integrating precise monitoring tools with solid analytical processes allows organizations to manage risks more efficiently.
Industry insights show that recent advancements in SecOps merge automated alert systems with robust risk assessment methods to support secure operations. These developments simplify data analysis and improve resource management, enabling teams to maintain secure IT environments while addressing evolving challenges.
Gather Insights From SecOps Leaders on Best Approaches
SecOps leaders offer clear strategies on streamlining security operations and maintaining up-to-date monitoring practices. Their insights assist organizations in improving cybersecurity measures and aligning IT service protocols with overall business operations.
Industry experts stress the importance of established communication channels and standardized incident response processes. Their recommendations support a structured approach that helps firms manage emerging threats and sustain secure IT environments.
Prepare for the Future Trends in SecOps and Cybersecurity
Reviewing SecOps evolution over the next decade, this section assesses the impact of artificial intelligence while investigating machine learning in threat detection. It anticipates upcoming regulatory shifts, discusses cybersecurity threat predictions and responses, and guides teams on best practices in SecOps development.
Explore the Evolution of SecOps Over the Next Decade
SecOps is projected to transform over the next ten years as modern tools and real-time monitoring systems become more integrated into cybersecurity frameworks. Industry professionals predict that automation and advanced data analysis will drive a shift toward faster threat detection and more precise incident response, supporting stronger IT service management and secure operations.
This evolution encourages organizations to adjust their cybersecurity investments and refine operational strategies to meet emerging risks. Strategic planning and investment in advanced security technologies provide businesses with clear guidance for maintaining resilience in a rapidly changing cyber environment.
Assess the Impact of Artificial Intelligence in SecOps
Industry experts note that artificial intelligence plays a significant role in redefining SecOps through automated threat analysis and real-time alert processing. AI-driven tools help process security alerts rapidly, allowing teams to reduce manual workload while strengthening their cybersecurity framework.
SecOps teams benefit from using artificial intelligence to sift through large amounts of security data and pinpoint risk patterns effectively. The integration of machine learning techniques contributes to more accurate incident detection, empowering organizations to secure their IT environments and manage risk confidently.
Investigate the Role of Machine Learning in Threat Detection
Machine learning provides a powerful solution for SecOps teams by processing extensive security data and automatically identifying anomalies that may indicate potential risks. This technology enables professionals to analyze activity in real time and allocate resources for prompt threat detection in cybersecurity operations.
The integration of machine learning with traditional security measures leads to more focused threat analysis and rapid incident response. SecOps experts rely on these tools to sift through large amounts of network data, ensuring that even minor irregularities trigger a timely review to protect critical IT systems.
Anticipate Changes in Regulatory Landscapes Affecting SecOps
Regulatory changes continue to shape SecOps practices as organizations update their compliance measures and security protocols to meet emerging standards. IT teams adjust risk management strategies to stay current with new guidelines and maintain effective cybersecurity operations.
Business leaders benefit when security teams actively monitor regulatory shifts and revise operational procedures accordingly. Proactive audits and clear planning enable organizations to sustain compliance while protecting their digital assets and IT service infrastructure.
Discuss Predictions for Cybersecurity Threats and Responses
Industry analysts forecast that cybersecurity threats will intensify as adversaries adopt more advanced techniques and seek vulnerabilities in IT systems. SecOps teams are expected to update real-time monitoring and incident response protocols to maintain secure operations in modern security environments.
Experts predict that new forms of malware and multi-vector attacks will challenge existing safety measures within managed IT services. Security professionals recommend regular testing of response plans and increased integration of automated analysis tools to swiftly mitigate risk and keep operations secure.
Stay Updated With Best Practices in SecOps Development
SecOps professionals maintain a strong focus on continuous improvement by reviewing emerging research and integrating updated security methods into their protocols. They implement real-time monitoring systems and refined risk management frameworks that strengthen cybersecurity measures and support reliable IT service operations.
Staying informed with best practices involves regular system audits, targeted training sessions, and active participation in industry discussions. This proactive approach empowers teams to adjust operational procedures swiftly, resulting in improved threat detection and enhanced managed IT services.
Conclusion
SecOps plays a key role in strengthening system defenses by merging security measures with everyday IT operations. The framework supports continuous threat monitoring and rapid incident response through advanced tools and team collaboration. Organizations adopt these practices to optimize resource allocation and maintain steady adherence to evolving compliance standards. A unified security structure bolsters operational resilience and equips business owners to address emerging cybersecurity challenges effectively.