How to Implement Zero Trust Printing – Its Components
The Components of Zero Trust Printing
Highly regulated industries such as healthcare and legal organizations have been the first to adopt zero-trust printing practices, as they frequently handle confidential materials. Zero trust means implementing stringent security measures to protect sensitive information.
However, today we see a growing interest in zero trust printing from a wide variety of organizations and market verticals. If your business uses shared printers, you should consider adopting a zero-trust model to enhance your security posture.
Zero-trust print environments leverage zero trust principles to secure every aspect of the printing process. By integrating cloud print services and advanced print solutions from providers like Xerox and Canon, organizations can ensure their network security is robust. Zero-trust security isn’t just about securing individual devices; it extends to creating comprehensive zero trust environments. Embracing these zero trust networking practices can significantly improve cybersecurity across your print infrastructure.
Always Verify
Zero trust isn’t just a concept; it’s a security policy that can be applied to managed print technology to enhance document printing security. This is typically achieved by installing secure printing software, requiring users to swipe a programmed badge or card at a reader attached to the printer or enter a Personal Identification Number (PIN) into the keypad. Once the user is verified and authorized, they can select and release their print job.
Incorporating a secure cloud print feature on a shared printer or multifunction device helps protect sensitive data, preventing unauthorized access and potential data breaches. This approach is an extension of the zero trust network architecture philosophy, ensuring that printing means safeguarding confidential information.
Moreover, secure printing strategies offer additional benefits, such as reducing unintended printing, conserving paper, and cutting down on paper waste. In a hybrid workplace, integrating print management software as part of your zero trust architecture can significantly enhance your overall cyber security.
Provide Least Privileged Access with Segmentation
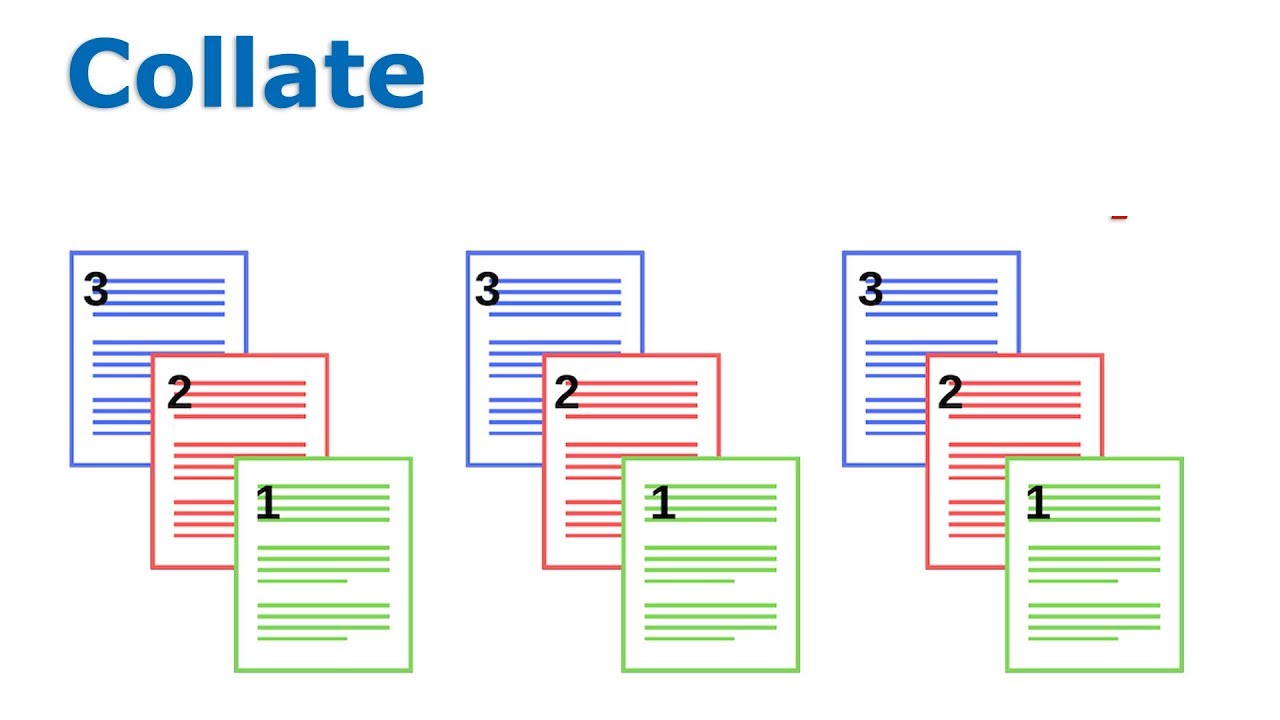
Unrestricted access to printers can pose significant security risks and lead to unnecessary costs. Securing your office print environment is crucial. By implementing secure printing technology, you can define and manage printing access for each user. This allows you to segment users and provide access only to the printers or multifunction devices they need.
For example, you might have a high-end printer designated for specialty marketing materials and product manuals. This printer may offer higher quality paper, various sizes, and additional binding features not found on standard office printers. Due to the higher cost per page, access to this printer can be restricted to users who regularly need to print these specialty materials.
Similarly, in organizations with multiple locations, most users only need access to printers at their physical location. However, some users, such as management or salespeople, may need access to printers at multiple locations. By segmenting access, you ensure that users can only use the printers necessary for their role, enhancing security and reducing costs.