Navigating the complexities of digital security can be a daunting task for any business leader. Effective cybersecurity solutions for businesses require more than just installing software; they demand a strategic, layered defense combining the right technology, expert services, and robust policies to protect your most valuable assets. This guide cuts through the technical jargon to provide a clear, actionable overview of the essential solutions needed to secure your company against modern online threats.
Building a Modern Cybersecurity Defense
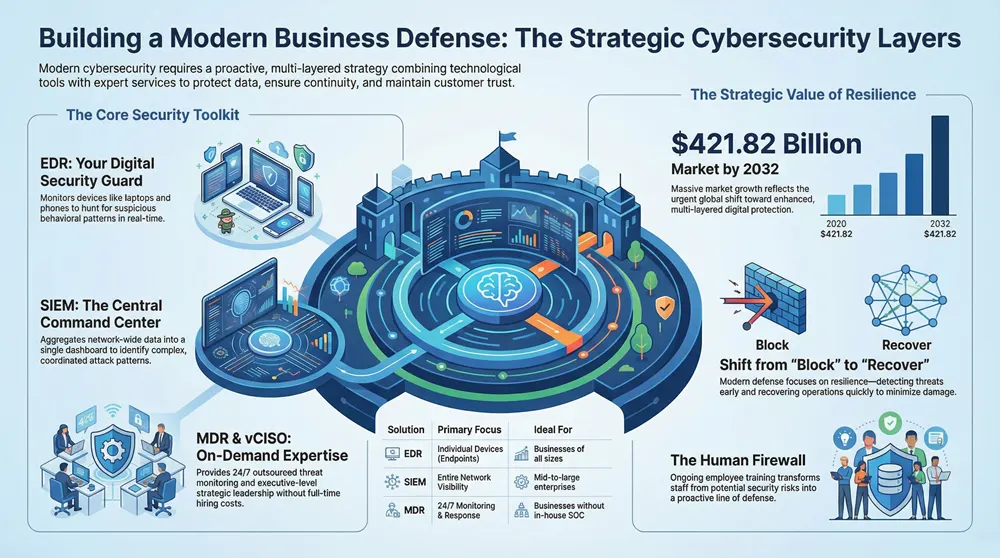
Securing a modern business demands a strategy that extends far beyond traditional antivirus and firewalls. As companies increasingly rely on digital operations, the potential entry points for attackers—known as the “attack surface”—expand significantly. This reality makes a proactive, multi-layered security plan essential for business survival and growth.
This article provides practical explanations of what each security solution does and why it matters to your daily operations. Understanding these core concepts is the first step toward making confident security decisions. To establish a baseline, a thorough cybersecurity risk assessment and management guide can help pinpoint your company’s unique vulnerabilities.

Why a Proactive Strategy Matters
Waiting to act until after a breach has occurred is a formula for financial and operational disaster. This reactive approach is no longer viable against sophisticated cyber threats. The consequences of a successful attack extend well beyond immediate financial losses.
A single security incident can trigger crippling operational downtime, cause long-term damage to your reputation, and rack up massive regulatory fines. Shifting to a proactive strategy turns cybersecurity from a confusing expense into a genuine business advantage.
Instead of only blocking attacks, a modern defense strategy focuses on resilience. It involves implementing systems to detect threats early, neutralize them swiftly, and recover operations quickly, minimizing damage to the business.
A robust cybersecurity strategy achieves several key objectives:
- Protecting Sensitive Data: Safeguarding customer information, financial records, and proprietary intellectual property is the primary goal.
- Ensuring Business Continuity: A strong defense prevents disruptions that can halt operations and impact revenue.
- Building Customer Trust: Demonstrating a commitment to security shows customers that their data is safe, reinforcing their confidence in your brand.
- Meeting Compliance Requirements: Many industries must adhere to strict data protection regulations, with significant penalties for non-compliance.
This guide provides the foundational knowledge to begin layering the right defenses for your specific business needs, protecting your assets, reputation, and the trust you’ve built with your customers.
Understanding Core Cybersecurity Solutions
To construct an effective defense, you must first understand the available tools. The field of cybersecurity solutions for businesses is filled with acronyms that can be overwhelming. The simplest approach is to view these solutions as specialists on your security team, each performing a unique and critical function.
A layered defense is a modern necessity. Cyber threats are highly sophisticated, and a single vulnerability is all an attacker needs. The market’s explosive growth reflects this reality. Valued at USD 203.86 billion in 2025, the global cybersecurity market is projected to reach USD 421.82 billion by 2032, driven by the urgent need for enhanced protection.
At-a-Glance Comparison of Key Cybersecurity Solutions
To clarify how these core services work together, the following table breaks down their primary roles, what they protect, and the businesses that benefit most from each.
| Solution | Primary Function | What It Protects | Ideal For |
|---|---|---|---|
| EDR | Detects & responds to threats on individual devices | Laptops, servers, mobile phones (endpoints) | Businesses of all sizes needing device-level security |
| SIEM | Centralizes & analyzes security data from the entire network | All network assets (firewalls, servers, apps) | Mid-to-large enterprises needing comprehensive network visibility |
| MDR | Provides 24/7 outsourced threat monitoring & response | The entire IT environment | Businesses lacking in-house security expertise or 24/7 coverage |
| vCISO | Offers strategic security leadership & compliance guidance | Business strategy, risk management, and compliance | SMBs needing executive-level guidance without the full-time cost |
This table provides a high-level overview, but understanding the purpose behind each solution is crucial for making the right investments to protect your company.
EDR: The Digital Security Guard on Duty
Think of Endpoint Detection and Response (EDR) as a highly vigilant security guard stationed at every company device—laptops, servers, and mobile phones. It surpasses traditional antivirus, which primarily scans for known malicious files. EDR functions as a behavioral analyst, actively hunting for suspicious activity, such as a program attempting unauthorized file encryption or an application sending data to an unusual server.
When EDR identifies a threat, it doesn’t just block it; it meticulously records every action, creating a forensic trail. Security professionals use this data to understand the attack methodology and prevent future incidents.
EDR is your first intelligent line of defense at your network’s most vulnerable points. It’s the difference between a simple burglar alarm and a full surveillance team that can identify, investigate, and neutralize a threat in real-time.
This capability is essential for stopping modern attacks like fileless malware and ransomware, which are designed to evade traditional signature-based defenses.
SIEM: The Central Command Center
While EDR protects individual endpoints, Security Information and Event Management (SIEM) serves as the central command center for your entire digital operation. It aggregates log data and security alerts from all sources—firewalls, servers, cloud applications, and EDR tools—into a single, unified dashboard. It functions like an air traffic controller for your network, monitoring all components simultaneously.
A SIEM’s true value lies in its ability to identify meaningful patterns within vast amounts of data. By correlating seemingly unrelated events from different systems, it can detect sophisticated, coordinated attacks. For example, it might connect a series of failed logins on a server with an unusual data download from a laptop, flagging a breach that would otherwise go unnoticed.
- Centralized Visibility: A single interface for monitoring security activity across your entire network.
- Threat Correlation: Connects isolated events to reveal complex attack campaigns.
- Compliance Reporting: Gathers and stores all necessary security logs, simplifying audits and compliance verification.
A SIEM acts as the brain of your security operations, providing the high-level intelligence required to interpret thousands of individual alerts.
MDR: Your Outsourced 24/7 Security Team
Realistically, most businesses cannot afford to establish and maintain a 24/7 in-house Security Operations Center (SOC). This is where Managed Detection and Response (MDR) provides a solution. An MDR provider offers both the technology (often including EDR and SIEM) and an elite team of security analysts who monitor your network around the clock.
Consider it a subscription-based, world-class cybersecurity team. They handle threat hunting, analysis, and incident response, allowing your internal IT staff to focus on strategic business initiatives. When a threat emerges, the MDR team investigates and contains it directly, rather than just sending an alert. This proactive, hands-on approach makes MDR one of the most effective cybersecurity solutions for businesses available today, delivering specialized expertise and 24/7 coverage at a fraction of the cost of an in-house team.
The Strategic Role of a Virtual CISO
A virtual CISO (vCISO) provides executive-level strategic security leadership without the significant expense of a full-time executive. This expert functions as a part-time member of your leadership team, responsible for developing your overall cybersecurity roadmap, creating policies, and ensuring regulatory compliance.
A vCISO helps answer critical business questions:
- Where are our most significant security risks?
- How should we prioritize our security budget?
- Are we compliant with regulations like GDPR or HIPAA?
This service bridges the gap between daily technical security and high-level business objectives. For small and mid-sized companies, a vCISO offers a practical balance of expert guidance and cost-effectiveness.
Of course, a complete security strategy must also defend your primary communication channels. You can learn more by exploring our guide on the best email security solutions available today. Furthermore, a key part of that defense involves implementing email authentication protocols like DKIM and DMARC to shut down common phishing and spoofing attacks before they ever reach your team.
Bolstering Your Defenses with Essential Security Services
Beyond foundational threat detection and response technologies, a truly resilient security posture depends on specialized, hands-on services. These services act as reinforcements, actively testing your defenses, protecting your most vulnerable assets, and providing a safety net for incidents. They are the essential layers that complete any serious cybersecurity solution for businesses.
A proactive stance has never been more critical. Market data shows that North America held a 43.41% share of the cybersecurity market in 2024, driven by stringent regulations and the high costs of breaches. This trend reflects a global understanding that security is a continuous effort, not a one-time setup. The global market is projected to reach USD 562.77 billion by 2032, as reported by Fortune Business Insights.
Penetration Testing: The “Ethical Hack”
How can you be certain your defenses will withstand a determined attacker? By hiring one to attempt a breach first. This is the principle behind Penetration Testing, also known as “pen testing” or “ethical hacking.” This service employs certified security experts to simulate a real cyberattack on your systems, applications, and networks.
Their objective is to find and exploit vulnerabilities just as a malicious actor would. By adopting an adversarial mindset, they uncover weaknesses—such as outdated software, misconfigured servers, or insecure code—before criminals do.
A penetration test is the ultimate security fire drill. It moves beyond theoretical risks and provides a real-world assessment of your weaknesses, giving you a clear, prioritized list of what needs to be fixed immediately.
This hands-on process uncovers hidden gaps that automated scanners cannot replicate, providing tangible proof of your security posture.
Securing Your Most Critical Entry Points
While internal network protection is crucial, many of today’s most damaging attacks originate from email inboxes and cloud accounts. Specialized security services are designed to secure these highly vulnerable entry points.
- Email Security Gateways: Email remains the primary vector for phishing scams, malware, and ransomware. An Email Security Gateway acts as an advanced checkpoint, inspecting every message for malicious content, spam, and phishing attempts before it reaches employees.
- Cloud Security (CASB): With more data and applications migrating to the cloud, visibility and control are paramount. A Cloud Access Security Broker (CASB) serves as a gatekeeper, enforcing security policies, detecting unauthorized data sharing, and protecting against cloud-specific threats.
These services are no longer optional add-ons; they are fundamental components for protecting modern communication and workflow channels.
Backup and Disaster Recovery: Your Ultimate Safety Net
No defense is 100% impenetrable. In the event of a disaster like a ransomware attack, the ability to recover quickly is paramount. This is where Backup and Disaster Recovery (BDR) becomes your most critical lifeline.
A modern BDR solution does more than just save file copies. It creates complete snapshots of your entire systems—applications, data, and configurations—and stores them securely off-site. If a catastrophic failure occurs, you can restore your entire operation to a point in time just before the incident, often within minutes or hours instead of days. This is the core of business continuity, ensuring a security breach does not become a business-ending event. For a deeper look, it’s worth exploring the benefits of managed security services.
Enabling Secure Work and Compliance
Finally, two key services help secure how your team works while ensuring legal and regulatory adherence. They help transform security from a constraint into a business enabler.
Virtual Private Networks (VPNs) create a secure, encrypted tunnel from a remote employee’s device to the company network. This is essential for protecting sensitive data when team members work from home, travel, or use public Wi-Fi. A business-grade VPN shields all traffic from unauthorized access, making remote work both safe and productive.
Compliance Management tools help you navigate the complex web of data protection laws like GDPR, HIPAA, and CCPA. These platforms automate the often-arduous process of tracking, managing, and reporting on compliance requirements. They provide a framework for conducting risk assessments, managing security policies, and demonstrating due diligence to auditors. This not only helps avoid substantial fines but also builds trust with customers who are increasingly concerned about how their data is handled.
How to Choose the Right Solutions for Your Business
Selecting the right security stack is not about acquiring every available tool; it’s about making strategic investments that align with your company’s specific circumstances. There is no one-size-fits-all cybersecurity solution for businesses; the most effective defense is tailored to your organization’s size, industry, and risk profile.
A customized approach ensures you receive optimal protection without investing in unnecessary features. The security infrastructure of a large enterprise would be excessive for a startup, just as a healthcare provider’s needs differ vastly from those of a construction firm. The goal is to match your defenses to your operational needs and threat level.
A Security Starter Pack for Small Businesses
For a small business, the priority is high-impact, low-cost protection where every dollar is maximized. The focus should be on neutralizing the most common and damaging attacks without introducing unmanageable complexity.
A solid starter pack should include these three essentials:
- Next-Generation Endpoint Protection: This is your front line against malware and ransomware targeting employee devices. Modern EDR is significantly more advanced than basic antivirus.
- Advanced Email Security: With phishing being the leading attack vector, a powerful email filter is non-negotiable for blocking malicious messages before they reach an inbox.
- Automated Cloud Backup and Recovery: This serves as your ultimate safety net. In the event of a successful attack, a reliable backup ensures rapid data and operational recovery.
These three pillars form a foundational defense that addresses the vast majority of threats a small business is likely to face.
This decision tree can help you visualize where to direct your efforts based on your immediate objectives.
As the flowchart illustrates, specific business needs—such as supporting remote workers or recovering from a breach—map directly to critical tools like VPNs and backups.
Scaling Security for Mid-Sized Businesses
As a business grows, so does its digital footprint and the complexity of securing it. At this stage, basic tools often become inadequate. An expanding team, a larger network, and increased data create new vulnerabilities that a starter pack cannot cover alone.
This is the point to begin layering more sophisticated tools. For instance, Security Information and Event Management (SIEM) platforms become indispensable for achieving a unified view across your entire network. A SIEM aggregates and analyzes log data from all systems, helping to identify coordinated attacks that might otherwise go undetected. The market reflects this need; the global cybersecurity market is expected to reach USD 351.92 billion by 2030, with SIEM tools being a major driver. You can review the full cybersecurity market report.
When your IT team can no longer manually chase down every alert and sift through endless log files, it’s time to bring in automation and centralized intelligence. This is the moment to consider a SIEM or a Managed Detection and Response (MDR) service to do the heavy lifting.
Integrated Ecosystems for Large Enterprises
At the enterprise level, operations demand a fully integrated security ecosystem. This typically includes a dedicated, in-house Security Operations Center (SOC) staffed with analysts who monitor for threats 24/7. The focus shifts from individual tools to a unified system where all components communicate and share threat intelligence in real-time.
High-level strategic guidance is equally critical. A virtual CISO (vCISO) or a full-time CISO is essential for directing the strategy, managing risk across the organization, and ensuring security goals align with business objectives.
Industry-Specific Security Needs
Finally, your industry significantly influences your security stack requirements. A company in a heavily regulated sector operates under a different set of rules than one in an unregulated field.
- Healthcare: Organizations handling patient data require HIPAA-compliant tools with robust encryption and strict access controls.
- Finance: Financial institutions must implement strong fraud detection, secure transaction processing, and solutions that meet PCI DSS compliance standards.
- Manufacturing: With the increasing use of IoT devices on the factory floor, securing operational technology (OT) from cyber-physical attacks is a top priority.
Aligning your security investments with your specific business context is the only way to build a defense that is both resilient and effective.
Putting Your Cybersecurity Strategy into Action

Knowing which cybersecurity solutions you need is the first step; integrating them into your business without causing disruption is the next. Moving from a plan to a real-world defense requires a clear roadmap that minimizes disruption and maximizes protection from day one. A deliberate, phased approach ensures that your new security measures are implemented smoothly and function as intended.
The first and most critical step is a thorough risk assessment. You cannot protect what you do not understand. This process involves identifying your most valuable digital assets—such as customer databases, financial records, and proprietary information—and then pinpointing the vulnerabilities that could put them at risk. This assessment forms the foundation of your entire strategy, guiding where to focus your efforts and budget to protect what matters most.
Vetting Your Security Partners
Once you understand your risks, the next step is to find the right partner to help address them. Choosing a security vendor is a significant decision, and asking the right questions upfront is key to a successful long-term partnership. When evaluating potential providers of cybersecurity solutions for businesses, it is essential to look beyond the sales pitch and understand their service delivery process.
Here are a few essential questions to ask:
- Incident Response Process: What are the specific steps you take when a threat is detected? Request a detailed walkthrough of their protocol, from initial alert to final resolution.
- Support Capabilities: What does 24/7 support truly entail? Will I be speaking with a qualified security analyst who can resolve my issue, or a call center agent who will simply create a ticket?
- Scalability and Future-Proofing: How will your services scale with my business? Can your solutions adapt to changes in our technology and the threat environment over the next three to five years?
The depth and clarity of their answers will reveal their expertise and commitment to client security.
Fostering a Security-Conscious Culture
Technology alone is not enough to secure your business. Your employees are a critical line of defense, but they can also be your greatest vulnerability. With a significant percentage of data breaches involving human error, employee training is an absolute necessity.
Your team is your human firewall. Effective, ongoing training transforms employees from potential security risks into proactive defenders, creating a culture where everyone feels responsible for protecting the company’s digital assets.
This training must be practical and continuous, not a one-time event. Focus on teaching staff how to identify phishing emails, use strong passwords, and handle sensitive data correctly. Regular reminders and simulated phishing tests are effective methods for keeping these best practices top of mind.
Executing a Phased Rollout Plan
Attempting to implement your entire security stack at once can lead to disruption and frustration. A phased rollout is a much smarter strategy, allowing for a smooth, manageable integration that does not halt daily operations.
Start with the highest-priority solutions identified in your risk assessment, such as endpoint security or email filtering. This allows your team to acclimate to one new system at a time, ensuring proper configuration and minimizing resistance. By breaking the implementation into smaller, controlled stages, you can execute your cybersecurity strategy with confidence and precision.
Measuring the ROI of Your Cybersecurity Investment
Every proposal for a new cybersecurity solution for businesses eventually faces the question from leadership: “What’s the return on this?” While security does not directly generate revenue, its value is immense. The key is to frame the discussion around cost avoidance rather than profit generation.
The most effective way to address ROI is to highlight the potential costs of a breach. This includes operational downtime, significant regulatory fines, legal expenses, and the high cost of incident response and system recovery. When this potential loss is compared to the predictable cost of proactive protection, the investment becomes a clear strategic imperative.
Calculating Hard and Soft ROI
The financial calculation is only part of the story. The “soft” ROI, though more difficult to quantify, is equally vital to the long-term health of your business and presents a compelling case.
These benefits include:
- Enhanced Customer Trust: Demonstrating a serious commitment to data protection builds customer loyalty and protects your brand reputation.
- Winning New Business: Strong security is often a prerequisite for securing contracts with enterprise clients and government agencies. It opens doors to new opportunities.
- Improved Operational Resilience: A well-defended business experiences fewer disruptions, leading to a more productive team and smoother operations that contribute to the bottom line.
The key is to present cybersecurity as a strategic business enabler, not just another line item expense. It’s not just a shield; it’s what protects the revenue-generating parts of your business and lets you grow without fear.
Ultimately, a solid security investment not only protects your current assets but also enables future growth by safeguarding your financial stability and reinforcing the trust necessary to expand your business for years to come.
Frequently Asked Questions About Business Cybersecurity
Navigating the complex world of security often raises important questions. Here are clear, direct answers to the queries we hear most often when helping companies implement the right cybersecurity solutions for businesses.
Where Should a Small Business with a Limited Budget Start?
A small business should focus on essential solutions that neutralize the most common threats cost-effectively. Your top priorities should be a quality endpoint security solution, a powerful email filter to block phishing attempts, and an automated cloud backup system for critical data. One of the most effective and affordable defenses is multi-factor authentication (MFA); implement it across every possible service.
What Is the Difference Between MDR and an In-House Security Team?
An in-house security team provides dedicated internal control but is extremely expensive to staff 24/7 with specialized experts like threat hunters and incident responders. Managed Detection and Response (MDR) is an outsourced service that delivers the same expert monitoring and response for a predictable subscription fee. This makes it a more cost-effective and scalable option for most small to mid-sized businesses.
An MDR service gives you immediate access to an elite security team and advanced technology, bypassing the immense cost and time required to build those capabilities internally.
How Often Should We Perform a Penetration Test?
As a general rule, a penetration test should be conducted at least annually. However, businesses in highly regulated industries like finance or healthcare, or those that frequently update applications and infrastructure, should test more often. In these cases, quarterly tests or an assessment after any major system change is a prudent measure to ensure no new vulnerabilities have been introduced.
Is a vCISO a Real Substitute for a Full-Time CISO?
Yes, for many small and mid-sized businesses, a virtual CISO (vCISO) is a strategic and effective alternative. A vCISO provides the same high-level guidance, policy development, and compliance oversight as a full-time executive but on a fractional basis that fits your budget. This model provides access to top-tier expertise without the high cost of an executive salary, making it a practical way to scale security leadership as you grow.
Building a resilient security posture requires the right strategy and the right partner. At 1-800 Office Solutions, we provide comprehensive cybersecurity services tailored to your business needs, from strategic vCISO guidance to 24/7 managed detection and response. Secure your operations and enable growth by exploring our full suite of cybersecurity solutions for businesses today.

