The Cybersecurity Question You Can’t Ignore
Your business generates security events every single second. When an employee logs in, when a file is accessed, when an unusual download happens, when a failed authentication attempt occurs. Each event is a data point. Thousands of them. And somewhere in that noise might be an attacker who’s already inside your network.

This is where SIEM comes in. But what exactly is it, and why should you care?
What Does SIEM Stand For?
SIEM stands for Security Information and Event Management. The concept, stripped down, is simple.
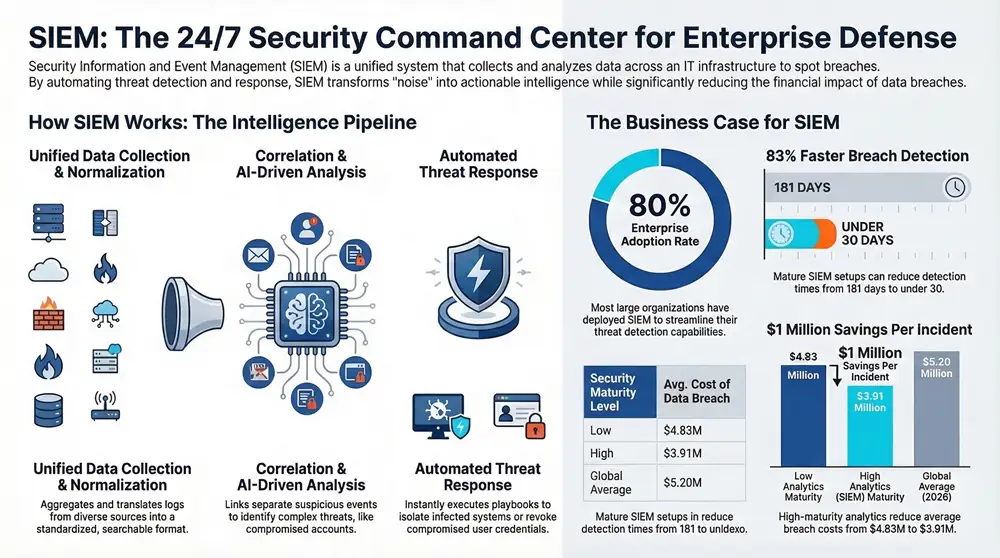
SIEM is a unified system that collects, analyzes, and responds to security events across your entire IT infrastructure. It gathers data from firewalls, servers, databases, endpoints, and cloud systems, then uses intelligence to spot patterns that indicate a potential breach.
Think of it as a security command center that never sleeps. It watches your network 24/7, correlates thousands of events, and alerts your team when something looks wrong. Without SIEM, you’d be trying to monitor security manually across dozens of disconnected tools. That’s not realistic at scale.
A Brief History of SIEM
SIEM didn’t appear overnight. It evolved from two separate security disciplines that eventually merged.
In the early 2000s, organizations had two distinct needs. They needed to collect and store logs from their systems — called Security Information Management (SIM). And they needed real-time monitoring and alerting for security events — called Security Event Management (SEM). Different tools, different teams.
Around 2005, vendors realized combining these capabilities made far more sense. The industry converged on unified SIEM platforms. Companies like Splunk, IBM QRadar, and others pioneered the modern approach. Today, SIEM has become the cornerstone of most security operations centers.
How Does SIEM Actually Work?
Understanding the mechanics helps you appreciate why SIEM matters. The process follows a clear pipeline.
Data Collection
SIEM begins by collecting data from every component of your infrastructure. Firewalls send logs. Servers report on user access. Cloud platforms submit API logs. Endpoints flag suspicious activity. This data flows into a central collection point.
The volume is massive. Enterprise environments often ingest millions of events per day.
Normalization
Here’s where things get interesting. Each source speaks a different language. Your Windows server logs look nothing like your Cisco firewall logs — different timestamps, different field names, different formats.
SIEM normalizes this data by parsing it into a common format. That standardization allows the system to correlate events across different sources. It’s the foundation for intelligent analysis.
Correlation and Analysis
This is the intelligence layer. SIEM uses rules — and sometimes machine learning — to connect dots. For example:
- User logs in from an IP address in China at 2 AM
- Same user suddenly accesses 500 files they’ve never touched
- Large data transfer from that user’s account happens 15 minutes later
Alone, any of these might be explainable. Together, they paint a clear picture of a compromised account. SIEM spots this correlation and raises an alert.
Alerting and Response
When SIEM detects a threat, it doesn’t sit on the information. It generates alerts and can automatically trigger responses. Some systems notify your security team instantly. Others can isolate a compromised machine or revoke permissions without waiting for a human.
Reporting and Compliance
SIEM maintains searchable archives of all events. When auditors come asking about security incidents, you have complete records. This is critical for regulatory compliance.
The Real Impact: Market Growth and Adoption
The numbers tell a compelling story about SIEM’s importance.
Market Size (2026): The global SIEM market was valued at approximately $8–10 billion in 2025 and continues expanding. Research firms project 2026 figures ranging from $8.6 billion to $14 billion, with growth rates of 12–16% annually through the early 2030s.
This isn’t random growth. It reflects a fundamental shift in how security-conscious organizations operate.
Enterprise Adoption: 80% of enterprises have deployed or plan to deploy SIEM platforms to streamline threat detection. Beyond that, 60% of organizations are expected to rely on Managed Security Service Providers for at least part of their security operations.
SIEM isn’t optional anymore. It’s becoming table stakes for serious organizations.
Key Features of Modern SIEM Platforms
Not all SIEM solutions are created equal. The best ones in 2026 share common capabilities.
Real-Time Analysis
Modern platforms analyze security events as they happen, not hours later. Speed difference is measured in minutes, sometimes seconds.
Automated Response
Top platforms don’t just alert you. They execute playbooks automatically — isolate systems, revoke credentials, disable accounts, or collect forensic data.
Machine Learning
AI-driven platforms learn what’s normal in your environment and detect anomalies more effectively than rule-based systems alone.
Scalability
Cloud-native SIEM solutions scale to handle millions of events without slowing down. On-premises systems require significant capacity planning.
Integration Capabilities
Modern platforms integrate with hundreds of data sources and third-party tools, creating a connected security ecosystem.
Behavior Analytics (UEBA)
Advanced solutions profile user behavior and detect when someone acts outside their normal patterns — a key signal of compromise.
The Business Case: Why SIEM Delivers ROI
For many organizations, the SIEM decision comes down to one question: does it save more than it costs?
The answer is increasingly yes — especially when you factor in breach prevention and damage reduction.
Detection Time Matters: The global average time to detect a breach is approximately 181 days, with containment taking another 60 days. Organizations with mature SOC capabilities cut this to under 30 days. Automated detection tools reduce response timelines by more than 50%. With AI-driven detection, some organizations achieve detection within 51 days versus 72 without automation.
That’s not just a technical achievement — that’s money. Organizations with strong SIEM and analytics capabilities reduce breach costs to roughly $3.91 million, compared to $4.83 million at organizations with low analytics maturity. That’s about $1 million in savings per incident.
When you factor in that the global average cost of a data breach is $5.2 million, SIEM isn’t an expense. It’s insurance that actually pays.
Real-World SIEM Use Cases

SIEM isn’t theoretical. It solves concrete problems every day.
Threat Detection and Response
This is SIEM’s core mission. Detect data theft in progress. Recognize malware infection. Identify when credentials are being used from impossible locations. SIEM catches these patterns and alerts your team in time to respond.
Compliance and Audit Requirements
Regulators demand proof that you have security controls in place. SIEM provides that evidence — tamper-proof logs, compliance reports, and documentation that you’re monitoring your environment. For regulated industries (healthcare, finance, retail), SIEM is often mandatory, not optional.
Incident Investigation
When an incident occurs, you need answers. Who accessed what? When? What did they do with that access? SIEM provides a complete audit trail. This forensic capability is invaluable in post-incident investigations and legal proceedings.
Threat Hunting
Your security team can use SIEM to proactively hunt for evidence of compromise — searching for lateral movement patterns, unusual system calls, or suspicious process execution. Many threats are found this way rather than through automated alerts.
Security Configuration Validation
SIEM lets you verify that your security controls actually work. Are firewalls blocking the right traffic? Are endpoints reporting properly? Are access controls enforced? SIEM gives you visibility into these operational questions.
Top SIEM Platforms in 2026
The SIEM market is competitive. These platforms lead the pack.
Splunk Enterprise Security
Splunk remains the market leader, excelling at data ingestion, flexible searching, and advanced analytics. The pricing reflects its capability — most suitable for large enterprises.
Microsoft Sentinel
Microsoft’s cloud-native SIEM has gained significant share. It integrates natively with Microsoft 365 and Azure, making it the natural choice for organizations deep in the Microsoft ecosystem. Consumption-based pricing appeals to growing organizations.
IBM QRadar
Powerful for large enterprises with complex environments. Strong machine learning capabilities and solid integration with other IBM security tools.
LogRhythm
Competes well in the mid-market with reasonable pricing and solid functionality. Their team focuses on ease of deployment — a real advantage for organizations without deep SIEM experience.
Elastic Security
A popular open-source and commercial platform. Appeals to organizations that want flexibility and prefer not to be locked into proprietary systems.
The right choice depends on your organization’s size, existing technology investments, and specific use cases.
Cloud SIEM vs. On-Premises SIEM
This decision has shifted from “cloud versus on-prem” to “what does your organization actually need.”
| Aspect | Cloud SIEM | On-Premises SIEM |
|---|---|---|
| Initial Investment | Low, subscription-based | High, hardware and licensing |
| Scalability | Automatic, elastic | Requires capacity planning |
| Maintenance | Vendor-managed | Your responsibility |
| Data Residency | Varies by provider | Complete control |
| Compliance | Check vendor certifications | You design controls |
| Best For | Growing organizations, multi-cloud | Regulated industries, strict data locality |
Most organizations are shifting toward cloud SIEM for its flexibility and reduced operational burden. Some regulated industries still prefer on-premises for data sovereignty reasons.
SIEM Challenges and How to Address Them
SIEM isn’t a magic solution. It comes with real challenges you need to manage.
Alert Fatigue
A poorly tuned SIEM generates thousands of alerts daily. Your team can’t respond to all of them. The fix is tuning, baseline refinement, and sometimes reducing data sources. Many organizations benefit from a managed SIEM provider who tunes the system based on deep expertise.
Cost and Complexity
SIEM solutions aren’t cheap, and they require expertise to deploy and manage. Organizations often underestimate staffing requirements. A competent SOC analyst is expensive and hard to find.
Data Integration Challenges
Not every system sends logs to SIEM out of the box. Some require custom integrations. Building these can be time-consuming and technically demanding.
False Positives
Rule-based SIEM detection generates false positives. Machine learning helps but isn’t perfect. Your team must investigate alerts and refine logic over time.
Retention and Storage
SIEM generates massive amounts of data. Retaining it for extended periods — required by some regulations — means significant storage costs. Organizations must balance retention requirements with budget constraints.
Is SIEM Right for Small and Mid-Sized Businesses?
For years, SIEM was exclusively an enterprise tool. That’s changed.
Cloud SIEM platforms have made it accessible to smaller organizations. The subscription model means you pay for what you use rather than investing millions upfront. And many SMBs are now subject to the same regulatory requirements as enterprises.
The real challenge for SMBs isn’t affording SIEM — it’s staffing the SOC. That’s why managed SIEM services have exploded in popularity. You get the technology and expert analysts without building an in-house security team.
For a 50-person business? You probably don’t need SIEM yet. For a 500-person organization? It’s increasingly hard to justify not having it.
How 1800 Office Solutions Delivers Managed SIEM
This is where we come in. At 1800 Office Solutions, we don’t believe SIEM should be a burden.
We deploy, manage, and monitor your SIEM platform so you don’t have to. Our team includes certified security analysts who understand threat detection, understand your business, and know how to tune SIEM for your environment.
Here’s what we handle:
- Architecture and deployment of cloud or on-premises SIEM
- Integration of data sources across your entire infrastructure
- Alert tuning and customization to reduce false positives
- 24/7 monitoring and threat detection
- Incident response support when alerts require investigation
- Quarterly reporting on security posture and trends
- Regular tuning and rule updates as threats evolve
We treat SIEM as a service, not a product. You get enterprise-grade security monitoring without the enterprise-grade complexity and cost.
Moving Forward with SIEM
The threat landscape doesn’t slow down. Neither should your detection capabilities.
SIEM has become a requirement for any organization that takes security seriously. It centralizes visibility, enables faster detection, and provides the audit trails regulators demand. The market is growing because the value isn’t hypothetical — it’s real.
If you’re not using SIEM yet, now is the time to evaluate it. If you already have it, the next question is whether it’s working hard enough. An under-tuned SIEM creates noise. A well-managed SIEM creates clarity.
That’s where we can help.
Ready to Improve Your Security Detection?
Let’s talk about how managed SIEM can work for your organization. Our team is ready to discuss your specific needs and help you detect threats faster.
Sources: SkyQuest Technology, ResearchAndMarkets, SentinelOne, CybersecurityTime, Total Assure. Updated March 2026.