If you’ve been around IT leadership or security conversations lately, you’ve probably heard the acronym SOC thrown around like it’s common knowledge. But what exactly is a Security Operations Center? More importantly, do you need one?
The answer is nuanced. Most businesses absolutely need the SOC function, but whether you build it in-house, outsource it, or find a hybrid model depends entirely on your company’s size, risk profile, and budget. Let’s cut through the jargon and talk about what SOCs actually do and why they matter.
The SOC Explained in Plain English
A Security Operations Center is your organization’s command center for cybersecurity. It’s staffed by people — and increasingly powered by AI tools — who monitor your systems 24/7, hunting for suspicious activity, responding to threats, and keeping detailed logs for compliance.

Think of it like a combination of a police dispatch center and a 24-hour security guard. The dispatch part catches the alert and routes it. The security guard investigates whether something’s actually wrong. And someone’s always watching, even at 3 a.m. on a Saturday.
Modern SOCs aren’t just reactive, either. They hunt for threats proactively, manage security tools, coordinate incident response, and maintain security metrics. They’re the nerve center of your defensive operations.
What a SOC Actually Does Every Day
In practice, SOC teams handle several critical functions:
- Monitor security events. Thousands of events flow into SOC tools every hour. Analysts triage these to separate signal from noise.
- Investigate incidents. When something looks suspicious, they dig deeper — tracing the attacker’s path, figuring out what got compromised, and scoping the damage.
- Respond to threats. They coordinate the immediate response: isolating compromised systems, notifying incident responders, and briefing leadership.
- Manage compliance. Many industries require logging and reporting. The SOC ensures those records exist and are accessible for audits.
- Hunt for threats. Rather than waiting for alerts, good SOCs proactively search their environment for signs of breach.
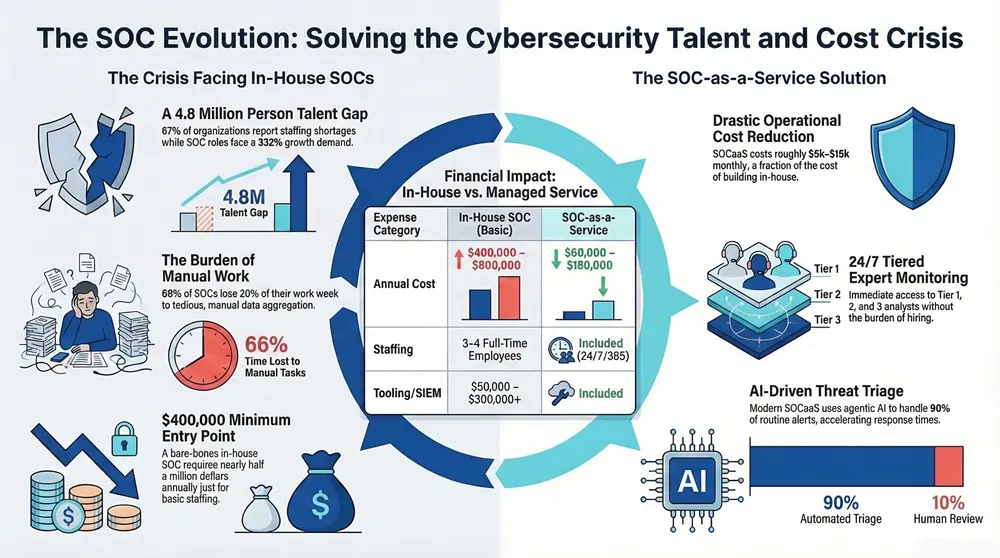
What often surprises people is how much time SOC analysts spend on manual work. According to recent research, 66% of SOCs lose 20% of their week just to data aggregation and correlation — analysts manually pulling data from different systems, trying to piece together what happened. It’s tedious, it’s error-prone, and it’s exactly the kind of work that AI and automation should eliminate.
The SOC Team Structure
SOCs don’t have a one-size-fits-all structure, but most follow a tiered model for good reason. It works, and it makes career progression clear.
Tier 1 Analysts: The Alert Handlers
Tier 1 is your frontline. They watch dashboards, acknowledge alerts, and make initial judgments — is this alert noise or real? They run basic checks, pull together initial context, and either resolve the issue or escalate it. Tier 1 doesn’t require a decade of experience, but it demands attention to detail and the ability to stay calm when alerts start flying.
Tier 2 Analysts: The Investigators
When something needs deeper investigation, Tier 2 takes over. These analysts know the infrastructure well. They can correlate data from multiple sources, understand attack techniques, and make judgment calls about whether something’s malicious. They’re usually starting to specialize — endpoint detection, network analysis, or similar focus areas.
Tier 3 Engineers: The Specialists
This is where deep expertise lives. Threat hunters, reverse engineers, or incident responders who handle the most complex cases. They also own SOC tools, tune detection rules, and improve processes. Tier 3 is smaller and more specialized than lower tiers.
SOC Manager
Someone has to coordinate all of this. The SOC manager handles staffing, budgeting, escalations, and metrics. They’re the bridge between the SOC and the rest of the organization.
Essential SOC Tools and Technologies
A SOC isn’t much without the right tools. Here’s what actually matters.
SIEM (Security Information and Event Management): The core tool. It collects events from your entire environment, normalizes them, and lets analysts search and correlate. Think of it as the database and search engine for everything that happens on your network.
SOAR (Security Orchestration, Automation and Response): SOAR tools automate routine response tasks. An alert comes in, and instead of an analyst manually running checks, the SOAR playbook automatically investigates, collects evidence, and recommends actions.
EDR (Endpoint Detection and Response): Endpoint-focused visibility. It sees what’s happening on each server and workstation. EDR is often where you catch attackers — they’re operating on actual systems, not just the network.
Threat Intelligence: SOCs need feeds of known malicious IPs, domains, file hashes, and attack patterns. Threat intel tools integrate this data so analysts can ask “Have we seen this hash before?” or “Is this IP associated with known attackers?”
Ticketing and Case Management: A system to track incidents from detection to resolution — often a custom workflow in your SIEM or a dedicated platform.
What’s worth noting is that SOCs are moving toward agentic AI. Instead of analysts manually reviewing 100 alerts, AI agents handle 90% of routine triaging, leaving humans to focus on strategic decisions. The math is compelling: fewer false positives getting escalated, faster response times, and analysts not burning out on repetitive work.
Types of SOCs: Which Approach Is Right for You?
You’ve got options for how to structure SOC capabilities.
In-House SOC
You build, staff, and operate everything yourself. Complete control, but serious capital investment and ongoing talent management. You’re responsible for hiring analysts, buying tools, maintaining infrastructure, and covering 24/7 with shift work.
Outsourced (Fully Managed)
You contract with a service provider to run the entire SOC. You get 24/7 coverage, expert staff, and mature processes. The tradeoff: you lose some control and need clear communication protocols with your vendor.
Hybrid Model
You handle parts of the SOC in-house — maybe Tier 1 and Tier 2 — while outsourcing Tier 3 or 24/7 coverage. This splits the workload and lets you focus on high-value work while someone else covers the on-call nights.
SOC-as-a-Service (SOCaaS)
The cloud-native version of outsourced SOC. You get SOC capabilities delivered as a service — cloud-based tools, pay-as-you-go pricing, and the ability to scale up or down. Increasingly popular with smaller and mid-market companies.
The Real Cost of a SOC
Let’s talk money — because cost is the reason most SMBs don’t have a traditional in-house SOC.
If you’re building in-house, you’re looking at:
- Tier 1 analysts at roughly $50,000–$75,000 per year
- Tier 2 analysts at $75,000–$120,000 per year
- Tier 3 engineers at $120,000–$180,000+ per year
- SOC manager salary plus benefits
- SIEM licensing (often $50,000–$300,000+ annually depending on volume)
- EDR, SOAR, and other tools (add another $100,000–$500,000+ per year)
- Infrastructure and maintenance
A bare-bones in-house SOC with 3–4 analysts and basic tooling runs $400,000–$600,000 per year. A mature SOC with 10+ analysts and comprehensive tools? $2–5 million annually, depending on infrastructure size.
This is why SOC-as-a-Service has exploded. For many companies, paying $5,000–$15,000 monthly for managed SOC services is dramatically cheaper than hiring and managing the team themselves.
Why the Talent Shortage Makes This Worse
Here’s the problem driving companies toward managed services: there aren’t enough SOC analysts to go around.
The Scale of the Shortage
According to the 2025 ISC2 Cybersecurity Workforce Study, the active global cybersecurity workforce stands at 5.5 million people — but there’s an unfilled gap of 4.8 million positions. Sixty-seven percent of organizations worldwide report staffing shortages.
Even more concerning, SOC analyst positions are expected to grow by 332% from 2023 to 2033. That’s massively outpacing the available talent pool. And the skills gap is widening — 63% of organizations cite critical skills shortages, up from 44% just a year ago.
The shortage creates a vicious cycle. New analysts need training. Experienced analysts are burning out from overwork and poor tooling. Salaries are climbing but can’t keep up with demand. For a mid-sized company trying to hire a SOC Tier 2 analyst in 2026, you’re competing against deep-pocketed enterprises. The average salary range for those roles is $107,000–$130,000, and good candidates field multiple offers.
The Rise of SOC-as-a-Service
This is where SOCaaS enters the picture as a pragmatic answer.
Market Growth
The SOC-as-a-Service market was valued at $8.44 billion in 2025 and is projected to reach $9.60 billion in 2026. The broader market is forecast to hit $25.32 billion by 2030, expanding at a 14.15% CAGR.
What does SOCaaS actually solve? First, it eliminates the talent problem — you’re not hiring. Your vendor handles recruiting, training, and retaining analysts. Second, it spreads cost across many customers, making 24/7 coverage affordable. Third, it usually includes modern tooling and automation that individual companies struggle to implement and maintain.
For a company with 100–500 employees, SOCaaS typically costs $5,000–$15,000 per month. Compare that to $400,000–$600,000 annually for a basic in-house SOC. The math is clear.
The tradeoff? You’re less hands-on with your own security operations. But for most mid-market companies, having expert 24/7 monitoring beats mediocre in-house coverage stretched too thin.
Key SOC Metrics That Actually Matter

If you’re building or evaluating a SOC, you need to measure performance. The two metrics everyone talks about are MTTD and MTTR.
MTTD (Mean Time to Detect): How long from when an attack starts until your SOC spots it. Measured in minutes or hours. Good SOCs detect most threats within 15–30 minutes. Great ones do it in single-digit minutes.
MTTR (Mean Time to Respond): How long from detection until the threat is contained — including investigation, decision-making, and action. A mature SOC should handle most incidents within 1–4 hours.
Beyond those two, track alert volume, false positive rate, and analyst capacity. If 46% of alerts are false positives, your team is drowning in noise. If analysts are running at 95% capacity, burnout is imminent.
The metrics that matter most are the ones connected to business impact: how much time does the SOC save by preventing incidents? How much faster do you recover when something does happen?
Building vs. Buying: Making the Right Call
Should you build an in-house SOC or buy SOCaaS?
Build in-house if: You have 1,000+ employees, significant regulatory requirements demanding local control, a mature security program already, and the budget to sustain it. Large enterprises often need the control and customization that comes with owning the function.
Buy SOCaaS if: You have fewer than 1,000 employees, want to focus your team on other security work, don’t have the budget for a dedicated SOC, or need to get SOC capabilities running quickly. Most mid-market companies fall here.
Go hybrid if: You want to own some parts but not all. Maybe you handle Tier 1 and 2 in-house while your vendor covers off-hours and Tier 3. This lets you keep your team engaged while outsourcing complexity.
How 1800 Office Solutions Provides SOC-as-a-Service
At 1800 Office Solutions, we provide managed SOC services designed specifically for mid-market businesses. We know the talent shortage is real, the costs are steep, and you need reliable 24/7 coverage without the headcount nightmare.
Here’s what we deliver:
- 24/7/365 monitoring and threat detection with Tier 1, 2, and 3 analysts available
- Modern SIEM and EDR tooling that we maintain and tune for your environment
- Incident response coordination and communication with your team
- Proactive threat hunting customized to your industry
- Monthly metrics and reporting so you know what’s happening in your environment
- Compliance logging for SOX, HIPAA, PCI-DSS, and other frameworks
We integrate with your existing tools — not replace them unnecessarily. We work with your internal IT and security teams, not around them. And we price it so you’re not spending more on SOC than on the rest of your security program.
The Bottom Line
A SOC is how you catch threats before they become breaches. Whether you build it in-house, outsource it, or find something in between, the function itself is non-negotiable for any company handling sensitive data or operating in regulated industries.
For most mid-market businesses in 2026, SOC-as-a-Service makes the most sense. You get expert monitoring, sidestep the talent shortage, and avoid the operational burden of staffing shifts and managing tools yourself.
The question isn’t whether you need SOC capabilities. It’s how you can get them efficiently and affordably. We’d be happy to walk you through what that looks like for your organization.
Ready to Explore SOC-as-a-Service?
1800 Office Solutions provides managed SOC services for mid-market companies. Enterprise-grade security monitoring — accessible and affordable.
Sources: ISC2 2025 Cybersecurity Workforce Study, Mordor Intelligence SOCaaS Market Report. Updated March 2026.
