Cybersecurity Solutions for Business: A Practical Guide to Protecting Your Company
Protecting your digital assets is a core business function, as critical to your company’s survival and growth as sales or finance. A single cyberattack can cripple operations, shatter customer trust, and lead to devastating financial losses. This guide provides a clear roadmap for business leaders to implement effective cybersecurity solutions, transforming a complex challenge into a manageable strategy that secures your bottom line. We will outline the practical layers of protection every organization needs to defend against modern threats.
Why Your Business Needs a Digital Fortress

Many business owners mistakenly believe, “We’re too small to be a target.” This is a dangerously outdated assumption. Attackers often view small and mid-sized businesses as ideal victims because they possess valuable data but frequently lack enterprise-level security. A successful breach can trigger severe consequences that extend far beyond the initial financial impact.
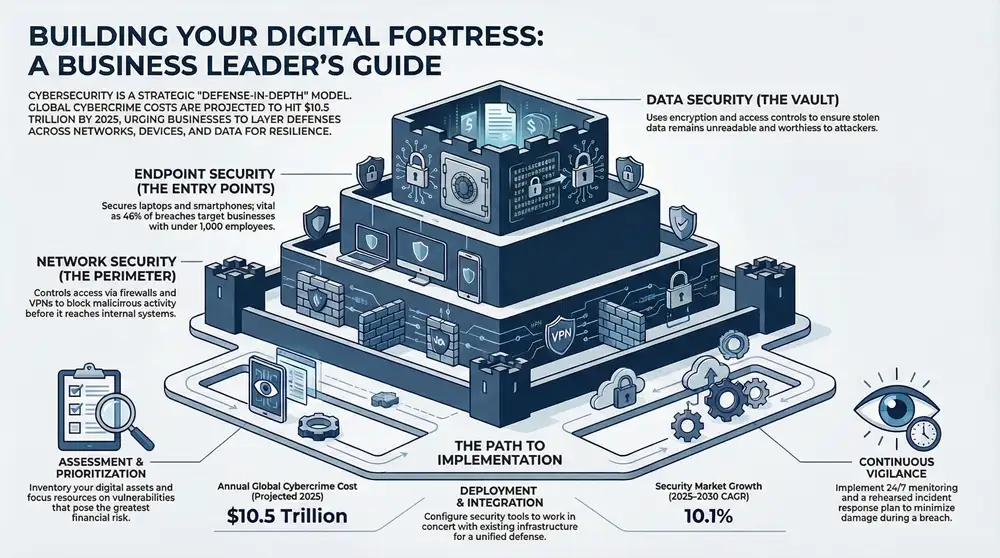
This is not an exaggeration; it is a measurable economic crisis. Global cybercrime costs are projected to reach USD 10.5 trillion annually by 2025. This staggering figure, reported by Cybersecurity Ventures, dwarfs the profits from the global illegal drug trade and highlights the widening gap between available security measures and criminal sophistication.
Beyond Firewalls: The Modern Security Imperative
Truly effective cybersecurity is much more than installing antivirus software. It is a strategic approach that integrates people, processes, and technology to create overlapping layers of defense. This “defense-in-depth” methodology ensures that if one security control fails, another is in place to stop an attack before it can cause harm.
At its heart, a business cybersecurity strategy is all about maintaining business continuity. It’s what ensures your operations can weather a digital storm, protect your most sensitive information, and preserve the hard-won trust you’ve built with your customers.
A robust security posture provides several key advantages that directly contribute to your company’s health and profitability:
- Protecting Your Reputation: A data breach can destroy customer trust overnight. That kind of damage is incredibly difficult, and sometimes impossible, to repair.
- Ensuring Operational Uptime: Cyberattacks don’t just steal data; they often grind your operations to a halt. Downtime means lost productivity and an inability to serve your clients.
- Safeguarding Critical Assets: Your intellectual property, customer lists, and financial records are the crown jewels of your business. They need Fort Knox-level protection.
- Meeting Compliance Requirements: Many industries are governed by strict data protection rules (like HIPAA for healthcare or PCI DSS for payments). The penalties for failing to comply can be severe.
Understanding Your Cybersecurity Arsenal
Implementing cybersecurity solutions can feel like learning a new language. Let’s simplify it. Imagine you are tasked with protecting your company’s physical headquarters. You would not just lock the front door; you would implement layers of security: a fence, guards, locked office doors, and a vault for your most valuable assets. Your digital fortress requires the same layered approach.
Effective cybersecurity is not a single tool. It is a collection of specialized solutions and processes working in concert, each designed to guard a specific part of your digital operations. We can break these down into essential categories that form the pillars of a solid defense.
Network Security: Your Digital Perimeter
Think of network security as the fence, gates, and security guards surrounding your headquarters. Its primary function is to control who and what gets in or out, creating a strong first line of defense. This layer inspects data moving across your network, identifying and blocking malicious activity before it reaches your internal systems.
Without it, your entire infrastructure is exposed. A classic example is a firewall, which acts as a digital gatekeeper enforcing access rules. Another key tool is a Virtual Private Network (VPN), which creates a secure, encrypted tunnel for remote employees. This ensures their connection to the business network is private and shielded from interception, even on public Wi-Fi.
The core tools here include:
- Firewalls: They monitor and filter network traffic based on predefined security rules, slamming the door on unauthorized access.
- Intrusion Detection and Prevention Systems (IDPS): These systems actively scan network traffic for sketchy patterns and can automatically shut down potential attacks in real-time.
- VPNs: Absolutely essential for any remote or hybrid workforce. VPNs encrypt internet connections to protect data as it travels between a remote user and the company network.
Endpoint Security: Securing Every Entry Point
If network security is the perimeter fence, endpoint security is locking every door and window. Endpoints are any devices connected to your network—laptops, desktops, servers, and smartphones. Each one is a potential entry point for an attacker. This is critical, as recent reports show that 46% of all cyber breaches target businesses with fewer than 1,000 employees, often through a compromised device.
These solutions are installed directly on each device to shield it from threats like malware and ransomware. Modern endpoint protection has evolved far beyond traditional antivirus software, using sophisticated techniques to detect and stop advanced attacks that would otherwise go unnoticed.
A single compromised laptop can give an attacker a foothold into your entire organization. Endpoint security ensures that even if a threat somehow slips past the network perimeter, it’s stopped dead at the device level before it can spread.
Cloud Security: Protecting Your Off-Site Assets
More businesses are storing data and running applications in the cloud. Think of this as using a high-tech, secure warehouse for your most valuable assets. Cloud security encompasses the policies, technologies, and controls you implement to protect that data, the applications using it, and the underlying infrastructure. It is essential to remember that cloud security is a shared responsibility.
While providers like Amazon Web Services or Microsoft Azure secure their data centers, you are responsible for securing how you use their services. This includes managing access, encrypting your data, and monitoring for unusual activity. Simple misconfigurations are a leading cause of cloud-related data breaches.
Data Security: The Last Line of Defense
Finally, data security is the vault inside your headquarters. It focuses on protecting the data itself, whether it is stored on a server (at rest), moving across the network (in transit), or being used by an application (in use). This is arguably the most critical layer, as your sensitive information—customer lists, financial records, and proprietary data—is the ultimate target for attackers.
The cornerstones of any data security strategy are encryption and access controls. Encryption scrambles data into unreadable code that is useless without the correct key. Access controls ensure only authorized individuals can view or modify specific information. Together, they make certain that even if an attacker breaches every other defense layer, the stolen data remains worthless.
To help visualize how these pieces fit together, here’s a quick rundown of the main categories.
Key Cybersecurity Solution Categories for Businesses
| Solution Category | Primary Function | Common Technologies & Examples |
|---|---|---|
| Network Security | Controls access to the network and blocks external threats at the perimeter. | Firewalls, VPNs, Intrusion Detection/Prevention Systems (IDPS) |
| Endpoint Security | Protects individual devices (laptops, servers, phones) from malware and attacks. | Antivirus (AV), Endpoint Detection & Response (EDR), Mobile Device Management (MDM) |
| Cloud Security | Secures data, applications, and infrastructure hosted in cloud environments. | Cloud Access Security Brokers (CASB), Cloud Workload Protection Platforms (CWPP) |
| Data Security | Protects the data itself through encryption, access control, and loss prevention. | Data Loss Prevention (DLP), Encryption tools, Identity and Access Management (IAM) |
Each of these categories plays a vital, distinct role. A strong security posture isn’t about picking one; it’s about layering them strategically to create a defense that’s tough to penetrate from any angle.
Your Step-by-Step Cybersecurity Implementation Plan
Knowing which cybersecurity solutions your business needs is one thing, but putting them into action is another challenge. A structured implementation plan turns your security strategy from a set of good ideas into a functional defense system.
This practical, five-stage roadmap will guide you through building a security program that is both effective and manageable, ensuring no critical steps are missed.
First, let’s look at how different security layers—from your network perimeter down to your core data—work together to create a solid defense.
This visual shows a layered approach. Think of it like securing a building: you have locks on the outside doors (network), security guards in the lobby (endpoints), keycard access to sensitive floors (cloud), and a safe for your most valuable assets (data). Each layer provides protection from a different angle.
Stage 1: Assessment and Discovery
You cannot protect what you do not know you have. The first and most critical stage is a thorough cybersecurity risk assessment. This process is the foundation for everything that follows. It involves creating a complete inventory of your digital assets—customer databases, financial records, proprietary software, and employee information.
Once you know what you have, the real work begins: identifying potential threats and vulnerabilities. Are your employees trained to spot phishing emails? Is your customer relationship management (CRM) software fully patched? Answering these questions provides a clear, honest picture of your current security posture.
For a deeper dive into this initial phase, you can learn more about how to structure a comprehensive cybersecurity risk assessment and management plan in our detailed guide.
Stage 2: Strategy and Prioritization
With a clear understanding of your risks, it is time to build a strategy. Not all vulnerabilities are created equal; a weakness that exposes sensitive customer data is far more critical than one affecting a non-essential internal tool. This stage is about prioritizing your efforts based on impact and likelihood.
Your goal is to focus your limited resources—time, budget, and personnel—on the threats that pose the greatest danger to your business. This risk-based approach ensures you achieve the most significant security improvements for your investment, rather than trying to fix everything at once.
Stage 3: Deployment and Integration
This is where the plan becomes a reality. In the deployment stage, you begin implementing the security controls and solutions identified in your strategy. This is more than just installing software; it requires careful configuration and integration to ensure all your new tools work together seamlessly.
For example, deploying a new firewall must be coordinated with your endpoint security settings to avoid conflicts that could leave you exposed. Key activities in this phase include:
- Configuring security tools according to best practices and your specific business needs.
- Establishing access controls to make sure employees only have access to the data they absolutely need for their jobs (nothing more).
- Integrating new solutions with your existing IT infrastructure to create a unified, cohesive defense system.
Stage 4: Continuous Monitoring and Maintenance
Cybersecurity is not a “set it and forget it” task. The threat environment changes constantly, with new attack methods emerging daily. Continuous monitoring is the process of actively watching your networks, systems, and applications for signs of suspicious activity. It is the digital equivalent of having a security team patrolling your premises 24/7.
Regular maintenance is just as crucial. This involves applying security patches, updating software, and reviewing security policies to ensure they remain effective against the latest threats.
Effective monitoring transforms your security from a static wall into a dynamic, responsive shield. It allows you to detect potential threats in real time, long before they can escalate into a full-blown breach.
Stage 5: Incident Response and Refinement
No matter how strong your defenses are, you must prepare for the possibility of a security incident. An incident response (IR) plan is your playbook for when a breach occurs, outlining the exact steps to take. A well-rehearsed IR plan minimizes damage, speeds up recovery, and ensures you meet any legal or regulatory notification requirements.
The plan should clearly define roles, communication protocols, and procedures for containing the threat and restoring business operations. After any incident, the final step is to analyze what went wrong, identify lessons learned, and use that insight to refine and strengthen your defenses for the future.
Choosing the Right Cybersecurity Partner

Implementing the right cybersecurity solutions is only half the battle. Technology is a powerful tool, but its true potential is unlocked by skilled experts. Selecting the right provider is a critical decision—they become an extension of your team and a guardian of your most valuable assets.
This decision goes beyond a sales pitch or a long list of features. A true partner works to understand your business goals, assesses your specific risk profile, and provides the expertise needed to navigate the complex threat environment. They help you transform a collection of security products into a cohesive, effective strategy.
Evaluating Expertise and Trustworthiness
When vetting potential cybersecurity partners, their experience and credentials must be a primary focus. Look for a team with a proven track record of protecting businesses of a similar size and in your industry. Real-world case studies and client testimonials provide valuable insight into their performance.
Do not just take their word for it—verify their technical expertise. A credible provider will hold industry-recognized certifications, which serve as clear proof of their skills and commitment to best practices.
Key credentials to look for include:
- CompTIA Security+: A foundational certification covering essential security functions.
- Certified Information Systems Security Professional (CISSP): A globally respected standard for senior-level security experts.
- Certified Ethical Hacker (CEH): Proves they have the skills to find and fix system vulnerabilities before attackers do.
These certifications indicate that the team has the validated knowledge to manage sophisticated cybersecurity solutions for business challenges.
Scrutinizing Technology and Service Agreements
A potential partner’s technology stack should be modern, comprehensive, and able to integrate with your existing infrastructure. Ask detailed questions about the tools they use for threat detection, endpoint protection, and network monitoring. A provider utilizing a diverse set of best-in-class tools is typically more adaptable than one tied to a single proprietary ecosystem.
Equally important is the Service Level Agreement (SLA). This legal document outlines the specific level of service you can expect. Review it carefully, focusing on guaranteed response times for critical incidents, uptime promises, and the process for escalating support tickets.
A strong SLA isn’t just a formality; it’s a commitment. It sets clear, measurable standards for performance and accountability, making sure you get the fast, effective support you need when an incident hits.
The Rise of Managed Security Services
Many businesses are discovering that simply purchasing security hardware and software is not enough. The market is shifting toward managed services, which provide the specialized expertise and continuous oversight required for a robust defense. The services segment of the cybersecurity market is projected to grow at the fastest rate, with a compound annual growth rate of 10.1% between 2025 and 2030, according to a report from MarketsandMarkets.
This trend makes it clear: effective security demands ongoing expert management.
A Managed Security Service Provider (MSSP) essentially becomes your dedicated security operations center. Instead of hiring, training, and retaining a costly in-house team, an MSSP provides 24/7 monitoring, threat hunting, and incident response. This model offers enterprise-grade protection at a predictable, scalable cost—a game-changer for many businesses. To see how this approach can secure your operations, you can learn more about the benefits of managed security services.
Ultimately, the right partner does not just sell you solutions—they invest in your success. They become a strategic advisor, helping you build a security program that not only protects your business today but is ready to adapt and defend against future threats.
Justifying Your Cybersecurity Investment
It is easy to view a cybersecurity proposal as merely an expense. This is a common and dangerous mistake. Smart business leaders treat security as a strategic investment that protects revenue, builds customer trust, and ensures operational continuity.
To secure the necessary budget, the conversation must shift from cost to return on investment (ROI). This involves translating technical controls into financial value, focusing on metrics that matter to leadership: risk reduction and cost avoidance. When you can clearly demonstrate how your security program prevents expensive disasters, it becomes an undeniable business asset.
Calculating the Value of Prevention
The most effective way to make your case is to calculate the potential cost of a breach you prevented. A single incident triggers a cascade of expenses, from regulatory fines and legal fees to the costs of customer notification and reputation repair. When a security solution stops an attack, it saves the company from absorbing these crippling losses.
For a real-world example, imagine a mid-sized e-commerce company invests in an advanced email security solution. Six months later, the system automatically quarantines a sophisticated phishing email targeting its finance department. If that email had succeeded, it could have led to a fraudulent wire transfer of $100,000.
In that scenario, the ROI isn’t some abstract concept. It’s a direct, six-figure loss that was completely avoided. By framing the investment against the specific, credible threats it neutralizes, you can prove its immense value.
This clear connection between investment and loss prevention transforms your security budget from a necessary evil into a vital insurance policy with a measurable payoff. Furthermore, effective security ensures your data remains protected, a critical topic we explore in our guide to cloud backup and data protection.
Quantifying Risk Reduction and Efficiency Gains
Beyond preventing major breaches, cybersecurity investments deliver daily value by lowering overall risk and streamlining operations. Every security control you implement—from multi-factor authentication to endpoint detection—reduces the probability of a successful attack. This reduction can be quantified and presented to leadership as a clear measure of progress.
Strong security tools also improve efficiency. Automated threat detection frees up your IT team from manually investigating every alert, allowing them to focus on projects that drive business growth. A centralized management dashboard provides a single, clear view of your security posture, saving hundreds of hours annually on compliance reporting.
The explosive growth of the global security market tells the same story. Valued between USD 203.86 billion and USD 227.59 billion recently, this market has skyrocketed from just USD 83.32 billion back in 2016. That growth is fueled by companies scrambling to defend themselves against attacks that threaten their core operations. You can find more insights on this expanding market on Data Bridge Market Research.
Ultimately, proving the value of your cybersecurity plan comes down to building a compelling business case. Focus on these key areas:
- Cost Avoidance: Detail the potential financial damage from specific threats your solutions are designed to stop.
- Risk Mitigation: Show with data how your security posture reduces the likelihood of an incident and protects the long-term health of the business.
- Operational Efficiency: Highlight how security tools automate tedious tasks, giving valuable time back to your team.
- Compliance Assurance: Explain how your investments help the company avoid steep regulatory fines and penalties.
Got Questions? Here Are Some Straight Answers About Business Cybersecurity
As you explore cybersecurity, many practical questions arise. To provide clarity, we have addressed some of the most common inquiries from business leaders.
What Is the First Step My Business Should Take to Improve Cybersecurity?
The absolute first step is a comprehensive risk assessment. You cannot protect what you do not know you have. This process involves identifying your most valuable digital assets—such as customer data, financial records, and intellectual property—and then determining how they could be threatened.
A thorough risk assessment provides a clear map of your vulnerabilities. It becomes the foundation for your entire security strategy, showing you exactly where to focus your efforts and budget to address the most significant risks first.
How Much Should a Small Business Budget for Cybersecurity?
There is no single magic number. The right budget depends on your industry, data sensitivity, and any compliance requirements. A general guideline is to allocate 3% to 6% of your total IT budget to security, but your risk assessment is a much better guide for spending.
For many businesses, managed security services are a more cost-effective option than building an in-house team. This approach provides access to top-tier experts and 24/7 monitoring for a predictable monthly fee, making enterprise-level security affordable.
It’s a huge mistake to think you’re too small to be a target. The data is clear: 46% of all cyber breaches hit businesses with fewer than 1,000 employees. Size is no defense.
Is Antivirus Software Enough to Keep My Business Safe?
No, not even close. Relying solely on antivirus software is a dangerously outdated strategy. While it is essential for protecting individual devices (endpoints), it is only one piece of a much larger puzzle. Today’s threats are too sophisticated for a single line of defense.
A robust security plan requires multiple layers working together. This “defense-in-depth” approach should also include:
- A strong network firewall to control inbound and outbound traffic.
- Advanced email security to filter out phishing scams.
- Regular, automated data backups for quick recovery.
- Consistent security awareness training for your team.
Each layer is designed to stop a different type of attack. Combining them creates a security posture that is far more resilient than any single tool could ever be.
What Is the Difference Between Cybersecurity and IT Security?
People often use these terms interchangeably, but they are not the same. IT security primarily focuses on protecting an organization’s internal data and systems from unauthorized access or damage. It is concerned with assets within your own network.
Cybersecurity is a broader concept. It includes everything IT security covers but expands to protect all digital assets from all types of digital threats, regardless of their location—on your local network, in the cloud, or on employee devices. Think of cybersecurity as the complete strategic plan for defending against every form of digital crime.
Protecting your business requires a proactive, multi-layered strategy managed by dedicated experts. At 1-800 Office Solutions, we deliver comprehensive managed cybersecurity services designed to defend your organization from modern threats, ensuring your operations remain secure and resilient. Secure your business with our expert cybersecurity solutions today.