Targeted Ransomware: Specific Industries and Systems Are Becoming Prime Targets for Ransomware Attacks
Targeted Ransomware
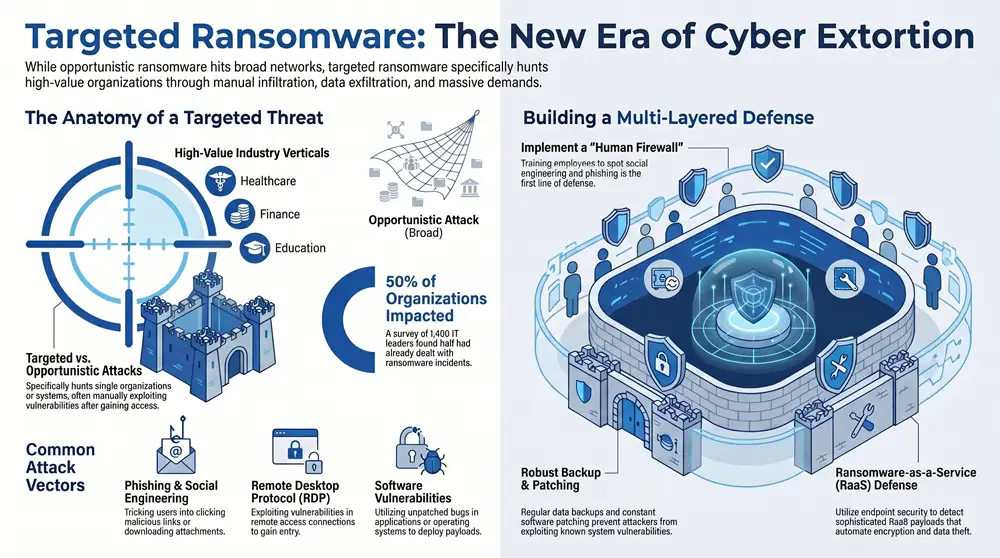
As a cybersecurity expert, it is important to be aware of the latest developments in the world of ransomware attacks. In particular, targeted ransomware attacks are becoming more and more frequent. These are attacks that are specifically aimed at certain industries or specific systems, and they can be particularly damaging if they succeed.
These attacks usually start with a malicious actor gaining access to a system, followed by a demand for a ransom in return for the release of the encrypted data. In some cases, the attackers will even use sophisticated techniques such as social engineering to increase their chances of success. The financial cost of such attacks can be massive, so it is essential to be aware of the growing trend of targeted ransomware attacks and to take appropriate measures to protect against them.
Introduction to Targeted Ransomware

Ransomware is malicious software deployed by cybercriminals to encrypt files, making them inaccessible, and demand a ransom for decryption. It has become a growing threat to organizations as attackers exploit vulnerabilities within cyber defenses, often targeting sensitive data. Organizations may be subject to a ransomware attack if they do not have robust endpoint security measures in place.
There are two main types of ransomware – opportunistic and targeted ransomware. Opportunistic ransomware is a type of malware used by cybercriminals to encrypt files on a large scale via phishing emails and malicious attachments.
Definition of Ransomware
Having discussed the different types of ransomware and how it works, it is important to understand the definition of ransomware. Ransomware is a type of malicious software, or malware, designed to block access to a computer system or its data until a ransom is paid. Attackers deploy ransomware to exploit a system’s vulnerabilities within the organization’s security measures, often targeting critical infrastructure, such as public services or healthcare organizations. Ransomware can come in many shapes and sizes, such as Ryuk, Wannacry, and REvil, and can deploy various payloads, such as encryption, exfiltration, or stolen data.
Ransomware works by encrypting all of the data or files on a system, then demanding a ransom payment in exchange for the decryption key. The ransom is typically demanded in cryptocurrency, such as Bitcoin, and can range between a few hundred to a few thousand dollars. Cybercriminals often operate in groups and use the dark web to launch ransomware attacks and to demand and receive ransom payments.
In some cases, the attackers will exfiltrate data before encrypting it, threatening to release the data publicly if the ransom is not paid.
Types of Ransomware
Moving on from the introduction to ransomware, let’s now look at different types of ransomware. Ransomware can come in many shapes and sizes, and can be split into two main groups: opportunistic and targeted ransomware attacks.
The main difference between the two is that opportunistic ransomware is deployed to larger, more widely spread networks, while targeted ransomware specifically targets a single organization or individual.
- Opportunistic ransomware attack:
- This type of ransomware is often distributed through phishing emails, malicious websites, email attachments, or even via vulnerable remote desktop protocol (RDP) connections.
- Attackers will deploy this type of ransomware to as many devices and networks as possible.
- The goal of this type of attack is to infect as many computers as possible, in the hopes that at least some of the victims will pay the ransom.
- Targeted ransomware attack:
- This type of ransomware is often deployed after malicious actors have gained access to the target’s network, usually through exploiting vulnerabilities within the system, or through phishing emails and social engineering.
- Attackers will deploy this type of ransomware to specific networks or systems, such as servers, databases, and other critical infrastructure.
How Ransomware Works
Having established what ransomware is and its various forms, it is now important to understand how ransomware works. A ransomware attack is a type of malicious attack in which a cybercriminal uses ransomware to extort money from the victim by encrypting their data and demanding a ransom payment for decryption.
Ransomware is a type of malware that is deployed by attackers to encrypt data on a target system using a strong encryption algorithm. By encrypting the data, the attackers render it inaccessible to the victim and demand a ransom payment in exchange for the decryption key that is necessary to restore the data.
Ransomware can be deployed through various attack vectors, such as email attachments, malicious websites, and vulnerable systems. Cybercriminals often use phishing emails and other social engineering techniques to trick victims into clicking malicious links or downloading malicious files. Once the ransomware is deployed on the system, it can spread quickly, encrypting the data on the system as well as any connected networks, and the victim may be presented with a ransom demand.
Organizations are also vulnerable to targeted ransomware attacks, which are more sophisticated in nature. Targeted ransomware attacks often target specific organizations and may be deployed through more sophisticated methods, such as exploiting vulnerabilities within the organization’s systems or using remote desktop protocols.
Who Is at Risk of Targeted Ransomware?
Ransomware is malicious software deployed by cybercriminals to encrypt files and demand a ransom from victims in exchange for a decryption key. Ransomware attacks are often targeted at healthcare organizations, financial services, and educational institutions due to their reliance on technology and the large amount of sensitive data they possess.
Cybercriminals may use phishing emails, malicious attachments, and vulnerabilities within remote desktop protocols to deploy ransomware. Recently, ransomware attacks such as WannaCry and Revil have affected 150 countries, extorting victims to pay a ransom in Bitcoin to restore their data.
Healthcare Organizations
The healthcare sector is particularly vulnerable to targeted ransomware attacks, as malicious actors have become increasingly adept at exploiting vulnerabilities within critical infrastructure. Healthcare organizations are often targeted based on their ability to pay a ransom, as failure to do so can have devastating consequences for their patients. In 2020, a ransomware attack affected a large retail company, leading to the exfiltration of data from more than 150 countries. This attack was an example of an opportunistic and targeted ransomware attack, as the malicious software was designed to encrypt certain files and demand a ransom in return for a private key used to restore the data.
Organizations in the healthcare sector rely heavily on the security of their data, as any ransomware-related incident can lead to stolen data or employees being unable to work. Recent ransomware attacks such as REvil and Wannacry have demonstrated the far-reaching consequences of ransomware incidents, and have caused healthcare organizations to invest heavily in their cyber defenses.
The modern ransomware landscape is complex, and the ransomware used in attacks can come in many shapes and sizes. For example, the ransomware Ryuk has been used in a variety of attacks, ranging from opportunistic to highly targeted ones. The attackers behind Ryuk are part of a larger ransomware gang and are known to demand a ransom payment in Bitcoin.
Financial Services
It is clear that any organization, from healthcare to finance, can be the target of a ransomware attack. Financial services are particularly vulnerable to ransomware attacks due to their many access points, data-driven operations, and cyber defenses that are often not up to date. As such, financial services can be attractive targets for ransomware attacks carried out by malicious actors, often in the form of ransomware-as-a-service (RAAS).
Ransomware gangs often target financial services because of the large amounts of money that can be made by encrypting the data and demanding a ransom payment. In a ransomware attack, malicious software is deployed through an attack vector such as an email attachment or a vulnerability within the system. This type of malware encrypts the victims’ data, making it impossible for them to access it without the encryption key, which is only provided by the attacker after a ransom is paid.
Organizations in the financial services sector are vulnerable to ransomware attacks due to the fact that they often rely on outdated cyber defenses and have employees that are easily tricked into clicking malicious links or downloading email attachments. Additionally, the sector is highly reliant on business processes that are data-driven, making it easy for attackers to steal sensitive data or encrypt certain files.
Educational Institutions
Considering the potential damage of a targeted ransomware attack, it is essential to understand who is most at risk. Educational institutions in particular are frequent targets, as attackers capitalize on the vulnerability of employees and students who may not be aware of the risks posed by ransomware.
Attacks on educational institutions can be both opportunistic and targeted. In the opportunistic attacks, attackers use phishing emails or malicious software to deploy their ransomware. In targeted attacks, attackers often exploit vulnerabilities within the institution’s cyber defenses to gain access to sensitive data. These attacks are usually motivated by extortion, as attackers demand a ransom from the victims in order to restore the data.
In a recent ransomware incident, a U.S. retail company paid a ransom to a ransomware gang. The ransom was demanded in Bitcoin and the attack affected businesses in over 150 countries. In March 2021, a ransomware attack on a major U.S. healthcare organization forced employees to work remotely and left the organization dealing with ransomware-related disruptions in their business processes.
Ransomware comes in many shapes and sizes, from the infamous Wannacry to the relatively new Ryuk ransomware. As modern ransomware groups offer “Ransomware-as-a-Service,” the threat of targeted ransomware is likely to increase.
The Growing Threat of Ransomware
Ransomware has become one of the most prevalent security threats of modern times. Cybercriminals use ransomware to encrypt files and demand a ransom in exchange for the decryption key. These ransomware attacks can range from opportunistic to targeted ransomware attacks, and attackers are becoming increasingly sophisticated in their ransomware operations.
Ransomware gangs are actively targeting organizations of all shapes and sizes, from large retail companies to critical infrastructure and healthcare organizations. WannaCry and Ryuk are two of the most notorious types of ransomware, and have been used to attack victims in over 150 countries.
Increase in Ransomware Attacks
The growing threat of ransomware is undeniable. The number of ransomware attacks has increased exponentially over the past few years, and they have become one of the most pervasive security threats for both businesses and individuals. Attackers use ransomware to encrypt data and then demand a ransom payment in order to decrypt it. They exploit vulnerabilities within organizations to gain access to sensitive data, and often target organizations based on their ability to pay the ransom.
A survey of more than 1,400 IT decision-makers found that half of organizations had dealt with ransomware attacks in the past. In 2020, ransomware was used to target organizations in more than 150 countries, and the healthcare sector was the most affected. In March 2021, a retail company was hit with ransomware, resulting in the exfiltration of customer data.
Ransomware is no longer limited to opportunistic attacks. Cybercriminals are now deploying more sophisticated versions of ransomware, such as Ryuk, REvil, and WannaCry. These types of ransomware are often used to target businesses, encrypt their data, and demand a ransom payment. Cybercriminals have also employed a ‘ransomware-as-a-service’ (RAAS) model, allowing malicious actors to deploy ransomware without having to have the technical expertise to do so.
Impact of Ransomware on Businesses
The growing threat of ransomware is becoming increasingly alarming, as the impact of ransomware on businesses has become increasingly pervasive. From encrypting files and demanding a ransom to stealing and exfiltrating data, ransomware attacks have had a tremendous effect on organizations of all shapes and sizes.
Ransomware has become a major problem for businesses, as attackers often target organizations based on their ability to pay a ransom, backed up by their own cybersecurity measures, or lack thereof. As a result, the following industries have been hit particularly hard by ransomware attacks:
- U.S Services Sector: In 2020, U.S services sector, such as retail companies, education, and healthcare organizations, suffered the most ransomware attacks.
- Healthcare Organizations: Healthcare organizations are often targeted by ransomware attackers due to the criticality of their data and the potential for a high ransom payment.
- Education Sector: The education sector is a prime target for ransomware operators, with ransomware attacks on universities increasing significantly in 2020.
The sophistication of ransomware attacks is constantly evolving, with attackers using novel attack vectors such as phishing emails, malicious software, and remote desktop protocol vulnerabilities.
Growing Sophistication of Ransomware Attacks
The growing sophistication of ransomware attacks is alarming and is an example of how cybercriminals are rapidly advancing their methods of extortion. With ransomware, malicious actors encrypt files and demand a ransom payment to decrypt the data, and the threat of ransomware is becoming increasingly complex and widespread.
In particular, ransomware-as-a-service (RAAS) is becoming a popular option for cybercriminals who may lack the technical expertise to deploy ransomware. RAAS can be purchased on the dark web, and cybercriminals can deploy ransomware on their own victims.
Ransomware attacks have become increasingly sophisticated, with attackers exploiting vulnerabilities within organizations to gain access to sensitive data. Attackers are now deploying ransomware on large, targeted organizations, often offering victims a discount if they pay the ransom quickly. Modern ransomware can encrypt entire networks, and attackers often exfiltrate sensitive data before encryption, increasing the pressure on victims to pay a ransom.
Recent ransomware attacks have highlighted the importance of cyber defenses. In March 2021, a retail company suffered a ransomware attack that encrypted certain files and stole data. The attack affected more than 150 countries, and the company had to pay a ransom to get it back. The attack was a reminder of the importance of having data backups and endpoint security measures to protect against ransomware.
How Can Organizations Protect Themselves?
Organizations must take the necessary steps to protect themselves from cybercriminals, and these can include implementing security policies, training employees on cyber security, and utilizing cyber security software. Implementing policies that establish the procedures and guidelines for protecting the organization’s data and systems is an important first step.
Training employees on cyber security can help to ensure that everyone understands the importance of good cyber hygiene and how to spot potential malicious activities. Utilizing cyber security software is also essential, as it can provide users with an extra layer of protection. It can also detect ransomware attacks and other malicious activities, as well as provide encryption and decryption capabilities for data.
Implement Security Policies
With the growing threat of ransomware attacks, organizations must take proactive steps to protect their data and assets. The best way to do this is to implement security policies that aim to minimize the risk of a ransomware attack. By establishing effective security measures, organizations can reduce the chances of a successful attack and the associated financial losses.
Organizations should deploy strategies to protect against ransomware, such as:
- Establishing rules for data access and usage
- Grant access to data only to those who need it
- Establish data access rights to ensure data is used appropriately
- Establish technical controls to protect data from unauthorized access
- Establishing policies to ensure security software is up-to-date
- Ensure all security software is up-to-date and patched
- Establish policies to continuously monitor and update security software
- Establish rules to ensure end-users are aware of the latest security updates
Organizations should also focus on increasing employee awareness and knowledge about ransomware. Employees should be trained to identify potential threats, such as phishing emails, malicious attachments, and other types of malware. Additionally, they should be instructed on best practices for using company data and assets, as well as how to report suspicious activity.
Train Employees on Cyber Security
The growing threat of ransomware is a devastating reality that organizations must face. The best way to protect against a ransomware attack is to train employees on cyber security. By educating employees on cyber security best practices, organizations can reduce the potential of a ransomware attack. To effectively train employees on cyber security, it is important to go beyond simply teaching them basic security measures and instead focus on the types of ransomware attacks, their method of operation, and how to protect against them.
Employees need to be taught about the different types of ransomware, their attack vectors, and how to detect and respond to them. This includes understanding how ransomware operates, the types of malware it uses, and the potential vulnerabilities within the organization that could be exploited by attackers. Employees must also learn about the importance of data backups, endpoint security, and other cyber security measures that can be deployed to protect against ransomware attacks.
Utilize Cyber Security Software
The need to utilize cyber security software to protect against ransomware has become paramount in recent years. As ransomware operators become more savvy, the range of attack vectors available to them increases. Ransomware is a type of malicious software that infects a system and then encrypts files, often demanding a ransom payment for decryption. Depending on the type of ransomware, it can range from opportunistic and targeted ransomware attacks to more sophisticated and targeted campaigns.
Cybercriminals often target organizations with high-value data, such as critical infrastructure, healthcare organizations, and government agencies, as well as non-profit organizations and educational institutions.
Organizations must deploy cybersecurity software that is designed to detect, monitor and protect against ransomware attacks. Cybersecurity software provides organizations with automated protection from a wide range of threats, including malicious software, phishing emails, ransomware targets, and attack vectors. It also provides a layer of protection from ransomware demands by alerting organizations to suspicious activity.
Additionally, endpoint security solutions can help protect against ransomware by preventing malicious software from entering an organization’s network.
Organizations should also deploy backup solutions to protect their data. Data backups are essential to any organization’s security strategy and provide an additional level of protection from ransomware attacks.
Impact of Targeted Ransomware on Individuals
The potential loss of personal data, damaged reputation, and financial losses that an individual can suffer from a targeted ransomware attack are devastating. Cybercriminals take advantage of software vulnerabilities and malicious emails to deploy ransomware, a type of malware designed to encrypt files and demand a ransom payment before allowing victims to access their data. Recent ransomware incidents include Ryuk, WannaCry, and REvil, with victims ranging from large organizations to individuals.
Organizations rely on endpoint security and data backups to protect against ransomware, but the threat of ransomware-related financial losses is still a major concern.
Potential Loss of Personal Data
The potential loss of personal data that can result from a targeted ransomware attack is a particularly devastating consequence for individuals. Cybercriminals who deploy ransomware are typically motivated by extortion, with victims asked to pay a ransom to decrypt the files. This type of malicious software is often used as a form of financial fraud, as cybercriminals demand a ransom payment in order to restore the data.
Vulnerabilities within an organization’s cyber defenses can provide an opportunity for attackers to deploy ransomware, with employees tricked into downloading malicious attachments through phishing emails or opening malicious links. Once a ransomware incident has occurred, the attackers will typically demand a ransom payment in order to decrypt the encrypted data. This can be a particularly difficult situation for ransomware victims, with the attackers often threatening to publicly release the stolen data if they don’t pay.
Ransomware gangs have been known to target individuals and organizations of all shapes and sizes, from small businesses to large corporations. For instance, a ransomware attack known as WannaCry was used to target victims in 150 countries in 2017, while Ryuk ransomware was used to target a U.S. retail company in March 2021. This type of malware can have a devastating effect, with victims unable to access certain files until a ransom has been paid.
Damaged Reputation
The devastating impact of a targeted ransomware attack on individuals can extend far beyond the financial losses. Individuals may also suffer from a damaged reputation if the ransomware attack is made public, or sensitive personal data is exposed.
If the malicious actors behind a targeted ransomware attack reveal details of the incident, the reputation of the individual may be tarnished. The information released may include details of the ransom demand or the malware used in the attack. It can cause individuals to feel humiliated, embarrassed, and exposed.
Individuals may even be targeted by cybercriminals for extortion. During a ransomware attack, cybercriminals may demand payment to return stolen data or to prevent further encryption. Ransom demands can be sent through malicious emails or even via a dark web listing.
Victims of targeted ransomware attacks may be reluctant to report a cyber incident for fear of public backlash. They may fear that their reputation will be damaged if the attack is revealed, and they may feel ashamed that they paid a ransom demand.
In order to protect themselves, individuals should deploy robust cybersecurity measures such as endpoint security and data backups to defend against ransomware attacks. This can help to ensure that if a ransomware attack occurs, their data will remain secure and their reputation will remain intact.
Financial Losses
Hacking and cybercriminal tactics have become increasingly sophisticated and targeted ransomware is a particularly damaging form of attack. Financial losses are one of the most devastating impacts of these malicious activities, and organizations that have failed to properly protect themselves suffer the most.
Organizations are unable to access their data until they pay the ransom demanded by the attacker. This ransom can range from a few thousand dollars to hundreds of thousands of dollars. Many organizations do not have the funds to pay the ransom and are forced to shut down operations or try to restore their data from backups. This can result in a significant financial loss.
Organizations that have fallen victim to ransomware attacks also face financial losses due to lost productivity and reputational damage. Businesses may have to spend additional money to hire consultants and security professionals to help them restore their systems and protect their data.
Organizations are advised to deploy endpoint security solutions to prevent ransomware from infiltrating their systems. It is also important to backup data regularly and patch any software vulnerabilities that can be exploited by attackers. Additionally, organizations can protect themselves from ransomware attacks by training their employees on cyber security best practices, such as recognizing phishing emails and not downloading malicious software.
What to Do if You’re the Target of Ransomware
If you are the target of a ransomware attack, it is important to take the necessary steps to protect yourself. Ransomware is a type of malicious software that encrypts files on a device, making them inaccessible until a ransom is paid.
Cybercriminals often target organizations with vulnerabilities within their cyber defenses, taking advantage of their ability to deploy opportunistic and targeted ransomware attacks. Recent ransomware attacks have affected a variety of industries, including the services sector, education sector, and healthcare organizations.
To protect against ransomware, organizations should deploy endpoint security solutions and backup their data regularly.
Contact Law Enforcement
It’s essential to be prepared for the worst-case scenario when facing a ransomware attack. One of the primary steps to take when encountering a ransomware incident is to contact law enforcement. Doing so will not only help you investigate the attack, but also provide an opportunity to seek restitution.
The first step in contacting law enforcement is to identify the type of ransomware used and any other related information. This information can be collected from the system logs, malware analysis, and by understanding the attack vector. It’s important to collect this information before attempting to contact law enforcement, as they’ll need to understand how the attack was conducted.
Once the type of ransomware and attack vector are identified, the next step is to implement a data backup system. This will ensure that any encrypted data can be recovered without having to pay the ransom. Once a backup system is in place, the ransomware victims can then contact law enforcement to report the incident.
When contacting law enforcement, victims should provide as much information as possible, including any ransom demands, the type of ransomware used, and any other information related to the attack. This will help law enforcement to assess the situation and provide guidance on how to proceed.
Implement a Data Backup System
No one wants to experience the panic and frustration of dealing with a ransomware attack. With attackers becoming increasingly more sophisticated, organizations must be proactive in implementing a data backup system to protect their information from malicious actors.
A data backup system is essential for organizations to maintain a secure environment. It is a process of copying and archiving data so it can be restored in case of an attack or other data loss event. Backing up data helps organizations return to normal operations quickly, providing them with the ability to restore critical data from backups stored on a secure network or cloud. It also reduces the likelihood of paying a ransom if the data is encrypted by ransomware.
Organizations can deploy a variety of endpoint security measures to protect against ransomware. These include endpoint detection and response, which can detect threats before they reach the endpoint, and endpoint protection, which can detect malicious payloads before they are delivered to the endpoint.
Additionally, organizations should use security measures such as patching vulnerabilities within their systems, deploying firewalls and anti-malware software, and training employees to recognize phishing emails and other threats.
By implementing a data backup system, organizations can prepare for any type of ransomware attack and mitigate the damage caused by malicious actors.
Contact a Cyber Security Expert
When facing a ransomware attack, it is essential to contact a cybersecurity expert. Cybersecurity experts specialize in defending against malicious software and can help you prepare for future ransomware attacks. They can provide advice on how to protect your data, how to detect and respond to ransomware attacks, and what steps to take to minimize the damage and increase your chances of recovering data.
Cybersecurity experts can review your security measures and identify potential vulnerabilities within your systems. They can help you deploy endpoint security and other measures to protect against ransomware attacks. They can also provide recommendations on how to strengthen your cyber defenses and help you ensure that your employees are not exposed to malicious emails or email attachments.
Cybersecurity experts can help you understand the type of ransomware that has infected your systems and what type of malware was used to launch the attack. They can provide advice on the best course of action to take to restore the data, as well as the best ways to prevent future attacks. In some cases, they may be able to suggest a way to decrypt the files without having to pay the ransom.
Cybersecurity experts can also provide advice on how to protect yourself against ransomware in the future.
How to Stay Safe From Ransomware
To stay safe from ransomware, it is essential to deploy security measures such as installing anti-virus software and keeping systems and software up to date. Additionally, it is important to avoid opening unfamiliar links or emails. Cybercriminals often use malicious emails, known as phishing, or malicious links as an attack vector to target victims.
Opportunistic and targeted ransomware attacks are on the rise, with cybercriminals constantly creating new ransomware shapes and sizes. Wannacry and Ryuk are two examples of ransomware used in recent attacks.
Install Anti-Virus Software
Now that you know the potential consequences of a ransomware attack, it is important to take the steps necessary to prevent such an attack. Installing anti-virus software is one of the most important steps to take, as this type of software can help detect and block any malicious software that attempts to enter your system.
Anti-virus software works by scanning the data that enters your system, such as emails and downloads, for signs of malicious activity. It then takes steps to neutralize any potential threats by either blocking the malicious content or quarantining it. When a new type of ransomware is discovered, anti-virus software is updated to recognize it, allowing it to recognize and protect against future attacks.
It is important to ensure that the anti-virus software being used is up to date, as ransomware is constantly evolving to make itself more difficult to detect. Additionally, it is important to choose a reputable anti-virus provider, as some may not be as effective as they claim.
It is also important to ensure that any firewall security measures are enabled, as this will help to prevent malicious software from entering the system. Additionally, ensuring that any existing security measures are updated regularly can help to protect against any potential vulnerabilities.
Keep Software and Systems up to Date
In order to stay safe from ransomware, it is essential to keep software and systems up to date. Without regular updates, organizations can become vulnerable to ransomware attacks, leaving them open to exploitation by cybercriminals. To protect against ransomware, organizations need to ensure that all their systems have the latest security patches and that any software they are running is regularly updated.
In addition to this, organizations should deploy endpoint security solutions to protect against malicious software. Endpoint security solutions provide a layer of defense against ransomware, by detecting and blocking any malicious attempts to enter the system. They also provide the ability to detect and respond to ransomware attacks, as well as to protect against any sort of ransomware-related extortion attempts.
Organizations should also consider backup solutions for their critical infrastructure, as these can be used to recover any encrypted data in the event of a ransomware attack. By keeping regular backups, organizations can ensure that they can restore their data in the event of a ransomware incident. It is also important to ensure that any backups are kept securely and that they are regularly tested to ensure they can be successfully recovered.
Finally, organizations should ensure that their employees are aware of the risks posed by ransomware, and that they are trained to recognize and respond to potential ransomware threats.
Avoid Opening Unfamiliar Links or Emails
The stark reality is that ransomware can be one of the most devastating cyber threats of our time. To protect themselves, individuals and businesses must be vigilant with their security measures and take steps to avoid opening unfamiliar links or emails, which may contain ransomware payloads. These malicious emails, also known as phishing emails, often have a deceptive sender address and contain attachments or links to malicious websites, tricking users into downloading and running a ransomware attack.
One way to protect against ransomware is to train employees to recognize and report suspicious emails, attachments, or links. Security measures like two-factor authentication can also be deployed to protect against phishing attacks, as well as ensuring that endpoint security, such as firewalls and anti-malware tools, are up-to-date and constantly monitored. Organizations must take a proactive approach to their cybersecurity and keep an eye out for potential vulnerabilities across their networks.
Cybercriminals often exploit these vulnerabilities to gain access to a company’s systems and launch ransomware attacks. It is essential, therefore, to deploy endpoint security and regularly scan for malicious software that can be used to encrypt files. Backing up systems and data is also essential for organizations, as it can help to restore encrypted data without needing to pay a ransom.
Ransomware Attack Mitigation Strategies

Keeping software and systems up to date is an essential strategy to mitigate ransomware attacks. Recent ransomware strains have been exploiting vulnerabilities within applications, operating systems, and other critical infrastructure. Regularly patching these systems with the latest security updates can help prevent malicious actors from gaining access to a system. Organizations should also deploy endpoint security solutions to monitor and protect against ransomware’s attack vectors.
Implementing comprehensive security policies can help protect against opportunistic and targeted ransomware attacks. Organizations should enforce staff training on cyber security best practices, such as avoiding suspicious emails, links, and attachments.
Keep Software and Systems up to Date
The consequences of a successful ransomware attack can be devastating, and so it is essential to keep software and systems up to date. This involves patching any known vulnerabilities and updating systems regularly to ensure the most recent security measures are in place. Such updates should be monitored closely and quickly deployed when available as attackers can exploit existing vulnerabilities to gain access to systems.
Additionally, organizations should carefully consider the security measures they have in place and deploy additional measures if necessary. Endpoint security solutions, for example, can be used to detect and protect against ransomware, as well as other types of malicious software.
Companies should also deploy a comprehensive backup strategy to ensure that their data is protected in the event of a ransomware attack, as this can significantly reduce the impact of the attack. Lastly, organizations should educate their employees on the various ransomware attack vectors, such as phishing emails and malicious attachments, as this can help to reduce the likelihood of a successful ransomware attack.
Implement Comprehensive Security Policies
In order to effectively mitigate ransomware attacks, it is crucial to implement comprehensive security policies. Companies must create an infrastructure with comprehensive security capabilities, such as:
- Keeping Software and Systems Up to Date: Organizations must regularly update and patch their networks and devices, as well as regularly install security updates for all systems, applications, and software. This will help to protect against exploits that can be used by malicious attackers to gain access to the system and deploy ransomware.
- Utilizing Cyber Security Software: Organizations must deploy cybersecurity solutions such as firewalls, endpoint security, and antivirus software. These solutions provide protection against ransomware attacks by monitoring and analyzing network and system activity for suspicious activity, and can detect and alert against malicious ransomware payloads.
- Implementing Comprehensive Security Policies: Organizations must have clear policies and procedures in place to protect against ransomware attacks. These policies should include strategies such as user authentication, user access control, email security, web security, mobile device management, and data backup and recovery. These policies should be regularly reviewed and updated to ensure that they remain up to date and effective in defending against any new or emerging ransomware threats.
It is also important for organizations to ensure that their systems are protected from potential vulnerabilities within the network.
Utilize Cyber Security Software
Transitioning to the next step in staying safe from ransomware, businesses must consider utilizing cyber security software to help mitigate potential ransomware attacks. Cyber security software provides the ability to deploy endpoint security measures that can protect against ransomware’s attack vector. This can help by defending against opportunistic and targeted ransomware attacks, as well as zero-day threats.
Deploying a cyber security solution that has a focus on ransomware detection and response should be a top priority. Organizations should also ensure that their security measures are based on their ability to detect malicious software, ransomware-specific threats, and attack behaviours.
In addition, advanced cyber security solutions are designed to detect ransomware activities, such as encryption of files and the exfiltration of stolen data. This helps organizations detect ransomware before it can inflict damage and also provides the ability to respond quickly and effectively to a ransomware incident.
Organizations should also consider implementing a cyber security solution that provides them with the ability to restore their data in the event of a ransomware infection. This helps them avoid having to pay the ransom demand to get their data back. It also helps them reduce the risk of a repeat ransomware incident.
In summary, utilizing cyber security software is essential for organizations that want to protect themselves from ransomware attacks.
What Are the Legal Implications of a Ransomware Attack?
Criminal Law Implications: Cybercriminals that deploy ransomware attacks often target organizations in order to extort money in the form of ransom payment. Victims of ransomware are often asked to pay a ransom in order to get back their stolen data or for a decryption key to unlock their encrypted data. In the U.S., ransomware attackers face criminal charges and may even be subject to long jail sentences for their malicious activities.
Civil Law Implications: Organizations and individuals affected by ransomware can also pursue civil litigation in order to claim damages and in some cases, receive compensation.
Criminal Law Implications
From the technical mitigation strategies to prevent a ransomware attack, to the legal implications of such an attack, it is clear that ransomware has become a prominent threat to businesses and organizations. One of the primary legal implications of a ransomware attack is the criminal law implications.
Criminal law implications refer to the potential legal ramifications of the malicious activity, including the persons responsible for the attack. Such activity is often associated with criminal charges such as extortion, theft, computer fraud, and money laundering. The legal systems of many countries have specific laws that define cybercrime and the related legal implications.
In the United States, the Computer Fraud and Abuse Act (CFAA) is a federal law that criminalizes certain malicious online activity, including accessing a computer without authorization, traversing a computer network, and damaging a computer system. Furthermore, the CFAA also provides certain protections to victims of ransomware attacks and outlines the legal implications associated with the malicious activity.
The legal implications associated with ransomware attacks can vary depending on the country and the severity of the attack. In some cases, ransomware may be treated as a form of theft, and the attackers may be held liable for any damages caused by the attack. In other cases, the attackers may face criminal charges for their malicious activity.
Civil Law Implications
As the previous section discussed, ransomware attacks require a comprehensive, multi-layered strategy to mitigate damage and prevent future attacks. However, it is also important to consider the legal implications of a ransomware attack, particularly when it comes to civil law.
When it comes to civil law, victims of ransomware attacks may be able to seek damages from the attackers if they are able to identify the perpetrators. In the U.S., victims may be able to sue the attackers for tortious interference with a business contract or for breach of contract. In addition, victims may be able to seek damages for negligence if the attackers failed to take reasonable steps to protect data or systems they were responsible for.
Victims may also be able to seek damages for any financial losses incurred as a result of the attack, such as the cost of decrypting data, restoring systems, and lost revenue or profits. Additionally, they may be able to seek damages for pain and suffering if the attack caused emotional distress or anxiety.
Furthermore, victims may be able to seek damages from companies that failed to provide adequate security measures to protect their data and systems. This could include companies that failed to patch known vulnerabilities, failed to provide proper employee training, or failed to implement proper access controls.
Regulatory Implications
The potential legal implications of a ransomware attack are critical to understand, especially for organizations that may be targeted. Regulatory implications are an important factor to consider, as any business can be subject to various regulatory and compliance requirements. Depending on the jurisdiction, ransomware victims may be required to report an attack and pay the associated ransom demand.
Furthermore, organizations must ensure that they are taking the necessary steps in order to protect themselves from potential attacks. This includes deploying endpoint security, performing regular backups, and educating employees on phishing emails and other types of malicious software.
Organizations must adhere to strict security measures in order to protect against ransomware, based on their ability to defend against different shapes and sizes of ransomware attacks. This includes both opportunistic and targeted ransomware attacks, which often target critical infrastructure such as the U.S services sector, education sector, and healthcare organizations. According to a recent survey, half of organizations have dealt with ransomware attacks, yet only 7% of them have paid the ransom demand.
For organizations that decide to pay the ransom, they are encouraged to do so with caution, as there is no guarantee that the encrypted files will be restored. In one instance, a retail company paid the ransom demand but the attackers still exfiltrated the company’s stolen data.
The Future of Ransomware
The future of ransomware is intertwined with the impact of Artificial Intelligence and Machine Learning, which has increased the potential for automation in ransomware attacks. Cybercriminals are now able to target vulnerable organisations with greater sophistication, deploying complex ransomware that encrypts essential data and demands a ransom payment.
Malicious actors are now able to exploit weaknesses in both public and private sectors, from healthcare organisations to retail companies, leaving victims with no choice but to pay the ransom to restore the data.
Impact of Ai and Machine Learning
The implications of a ransomware attack are far-reaching, and the future of ransomware looks to be even more concerning. As AI and machine learning become more sophisticated, there will be an increased risk of automation in the way ransomware attackers operate and the potential consequences of a ransomware attack. Artificial intelligence and machine learning algorithms can be used to detect vulnerabilities in systems and networks, to identify targets, and to tailor malware to the specific vulnerabilities of the victim.
The growing sophistication of ransomware attacks has been seen in the recent surge of ransomware-as-a-service (RaaS). In RaaS, malware developers offer access to their malicious software as a service, allowing cybercriminals to deploy ransomware with little technical knowledge or resources. This increase in accessibility of ransomware has led to its widespread use by cybercriminals of all shapes and sizes.
Moreover, AI and machine learning can be used to ensure the encryption of files is difficult to break, and to make it extremely difficult for ransomware victims to gain access to their encrypted data without paying a ransom. AI and machine learning can also be used to make ransomware more difficult to detect, and to automate the extortion process.
Increased Risk of Automation
In the future, ransomware attacks may become more automated, with artificial intelligence and machine learning playing a major role in increased risk. Cybercriminals are increasingly using automation to launch opportunistic and targeted attacks, using malicious software to scan for vulnerable systems, encrypt files, and demand a ransom payment. Automation of ransomware attacks can be used to target critical infrastructure and public services, such as government agencies, healthcare organizations, and educational institutions. The healthcare sector is especially at risk, with a recent study indicating that more than half of organizations had dealt with ransomware attacks by May 2023.
Malicious actors often target victims based on their ability to pay a ransom. For example, a ransomware gang known as REvil demanded a retail company pay a ransom of $50 million in March 2021, and threatened to exfiltrate stolen data if the ransom was not paid. Beyond this, ransomware has been used in campaigns that affected over 150 countries, encrypting certain files and demanding a private key to restore the data.
Organizations need to be prepared for potential ransomware attacks by taking preventative measures, such as ensuring the implementation of endpoint security, patching vulnerabilities within their systems, and creating data backups.
Growing Sophistication of Ransomware Attacks
The growing sophistication of ransomware attacks has made them a major threat to organizations. Cybercriminals have become increasingly adept at developing and deploying ransomware in order to extort organizations by encrypting their data and demanding a ransom payment in return for the decryption key.
Ransomware is a type of malicious software that is used by attackers to exploit vulnerabilities within a system, allowing them to gain access and encrypt files, effectively holding the victim’s data hostage until a ransom is paid. This often takes the form of a ransomware demand, where victims are instructed to pay a ransom in order to get their data back.
Recent attacks have shown that ransomware gangs have become increasingly proficient in deploying a variety of ransomware variants, often targeting critical infrastructure and the services sector. In March 2021, a retail company was hit with a ransomware attack that resulted in the exfiltration of its sensitive data, with the attackers demanding a ransom in Bitcoin. The attack affected more than 150 countries and encrypted certain files, rendering them inaccessible without the attackers’ private key.
Organizations must be aware of the risks posed by the ever-evolving sophistication of ransomware attacks.
Conclusion
Targeted ransomware attacks are an ever-evolving threat, and organizations need to be aware of the risks and take appropriate steps to protect themselves. Cybersecurity experts should be consulted to develop effective mitigation strategies, such as patching systems regularly, backing up data, and setting up access control.
It is also important to understand the legal implications of such attacks, as this can significantly impact both businesses and individuals. By taking preventative steps, organizations can reduce their chances of being the target of a ransomware attack and minimize the potential damage.